
The security event highlights of Zero Time Technology for this month have begun! According to statistics from multiple blockchain security monitoring platforms, the overall security situation in the cryptocurrency field in February 2026 was stable, but with prominent risks: The total losses due to security incidents that month were approximately $228 million, of which losses related to hacker attacks and contract vulnerabilities accounted for about $126 million, and losses related to phishing scams and Rug Pulls accounted for about $102 million. There were 18 reported protocol hacking incidents, with losses down by 9.2% compared to the previous month; 13 cases of phishing and authorization hijacking scams occurred, accounting for 41.9% of the total incidents that month, with several AI impersonation phishing incidents leading to significant losses, becoming the main cause for the rise in scam-related losses. Hacker organizations have shifted their focus to low-cost, high-reward social engineering attacks, combining AI-generated page phishing techniques, making individual investors and small projects the primary targets.
Hacker Attacks
Typical security incidents 6
• CrossCurve Cross-Chain Bridge Contract Verification Vulnerability Attack
Loss Amount: Approximately $3 million
Incident Details: From February 1 to February 2, the decentralized cross-chain protocol CrossCurve was attacked by hackers, who exploited a gateway verification bypass vulnerability in the expressExecute function of the ReceiverAxelar contract to forge cross-chain messages, unauthorizedly unlocking and stealing tokens from the protocol's PortalV2 contract, involving multiple chains, with a total loss of approximately $3 million. After the incident, the CrossCurve team urgently suspended cross-chain services, fixed the vulnerability, and published 10 addresses that received the stolen tokens, proposing a plan to return funds within 72 hours for a 10% reward; the situation has been successfully controlled, and some stolen EYWA tokens are unable to circulate due to exchange freezes.
• Vibe Coding Smart Contract AI Code Vulnerability Attack (Moonwell Protocol)
Loss Amount: Approximately $1.78 million
Incident Details: On February 18, the DeFi protocol Moonwell was attacked by hackers, primarily due to a fatal vulnerability in the smart contract code generated by Claude Opus 4.6, which incorrectly set the price of cbETH assets at $1.12 (actual price around $2200). The hackers exploited this price deviation for excessive borrowing, causing a loss of approximately $1.78 million. Security researchers revealed this incident as the first on-chain security incident caused by Vibe Coding in history. After the incident, the project team removed the relevant contracts, initiated a vulnerability repair, and strengthened the manual audit process for AI-generated code.
• YieldBloxDAO Oracle Manipulation Attack
Loss Amount: Approximately $10 million
Incident Details: On February 21, the Stellar chain lending protocol YieldBloxDAO was attacked by hackers, who manipulated the underlying liquidity token prices, using oracle price feed anomalies to achieve malicious excessive borrowing, resulting in an asset loss of about $10 million. After the incident, the project team suspended protocol services and coordinated with security agencies to trace assets and address vulnerabilities.
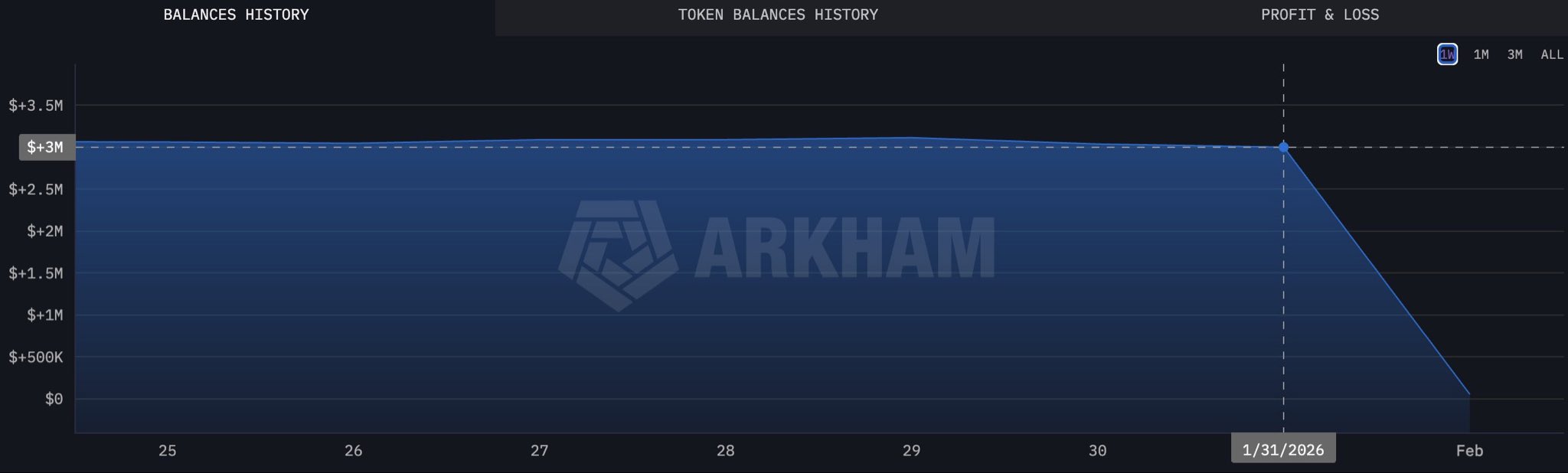
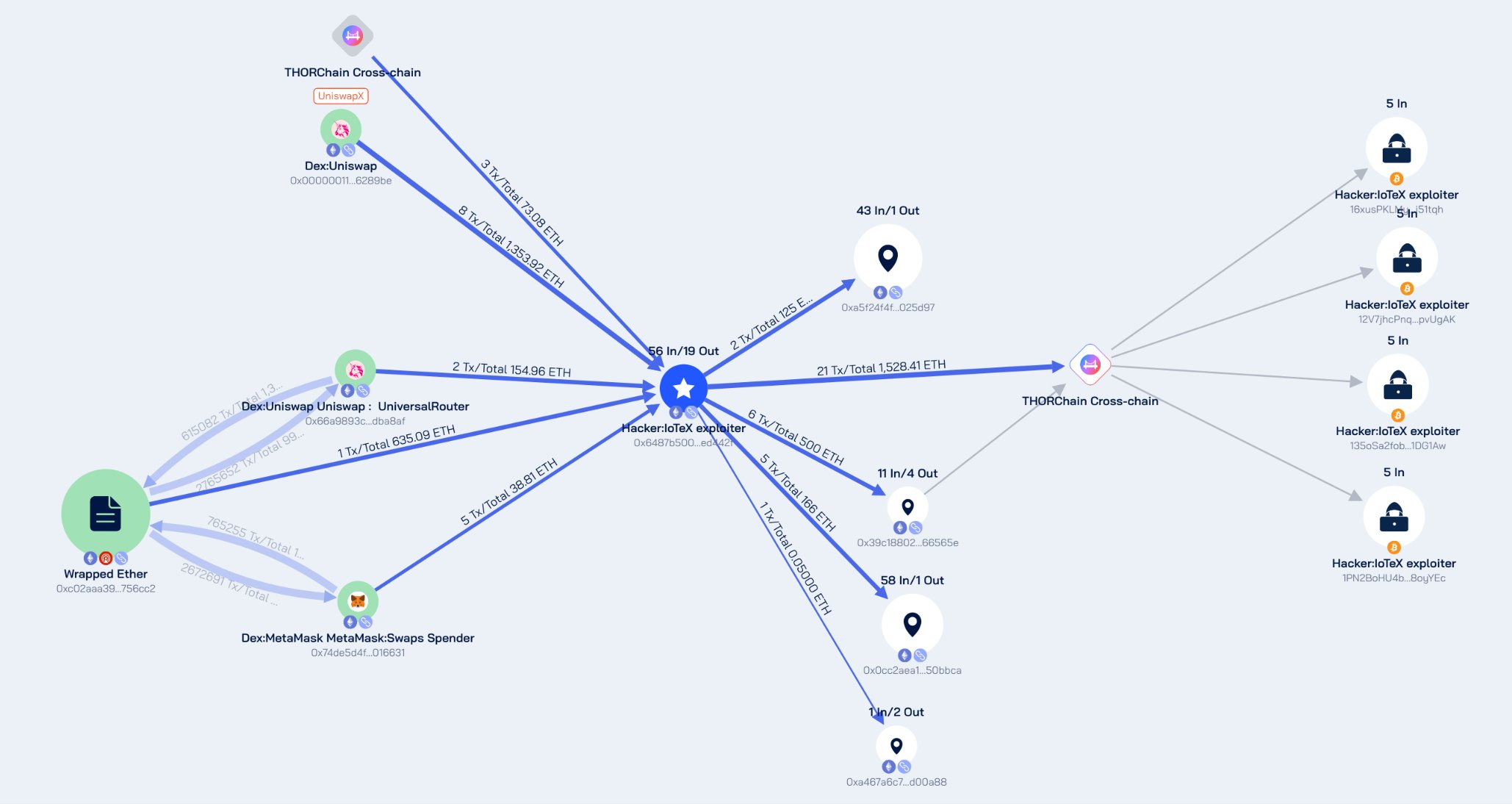
• IoTeX Token Vault Private Key Leak Attack
Loss Amount: Approximately $4.4 million
Incident Details: On February 21, the IoTeX ecosystem's ioTube cross-chain bridge encountered a hacker attack. The attackers obtained the private key of the Ethereum side validator owner, successfully breaching the contracts related to the cross-chain bridge, stealing various crypto assets from the pool. The IoTeX official issued multiple updates confirming that the actual loss from this attack was about $4.4 million, of which 99.5% of the abnormal minting has been intercepted or permanently frozen. After the incident, the project team urgently suspended the cross-chain bridge and related trading functions, initiated a mainnet version upgrade, blacklisted 29 malicious addresses, and cooperated with the FBI and multiple law enforcement agencies for global asset tracking, promising 100% compensation for affected users; full operations have now resumed.
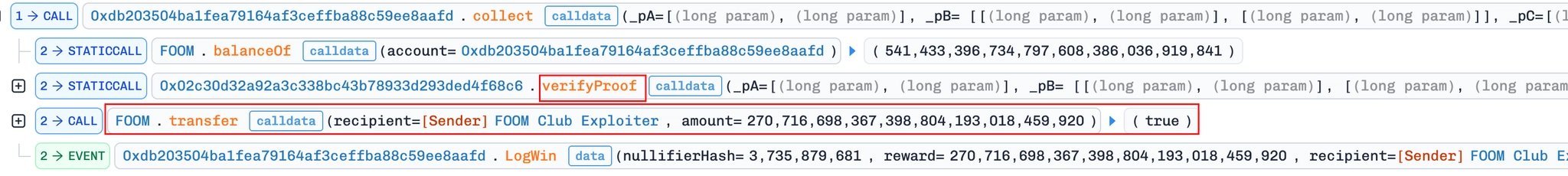
• FOOMCASH Imitation Attack Incident
Loss Amount: Approximately $2.26 million
Incident Details: On February 26, the FOOMCASH project on the Base chain and Ethereum chain faced an imitation attack (copycat attack), where the attackers used a zkSNARK verification key configuration error similar to the previous Veil Cash incident (improper Groth16 verifier parameter settings) to successfully forge proofs and steal large amounts of tokens. Among them, the Base chain lost about $427,000, and the Ethereum chain lost about $1.833 million (some funds were reportedly rescued by white hats), with a total loss of approximately $2.26 million. After the incident, the project team urgently suspended related services and launched an investigation.

• Seneca DeFi Protocol Arbitrary Call Vulnerability Attack
Loss Amount: Approximately $6.5 million
Incident Details: On February 28, the DeFi protocol Seneca was attacked by hackers due to an arbitrary call vulnerability, with preliminary estimates indicating losses exceeding 1900 ETH, valued at approximately $6.5 million. After the attack, the address marked as the SenecaUSD hacker returned 1537 ETH (about $5.3 million) to the Seneca deployer's address, while the remaining 300 ETH (about $1.04 million) was transferred to a new address; the project team is currently conducting vulnerability fixes and asset verifications.
Rug Pull / Phishing Scams
Typical security incidents 8
(1) On February 10, victims from addresses starting with 0x6825 signed a malicious “increaseAllowance” transaction on BSC, resulting in a loss of $118,785 in BUSD. Most people pay attention to authorization signatures and approval requests, but “increaseAllowance” is actually the same trap, just with a less common name.
(2) On February 17, address poisoning/similar recipient attacks struck again. On Ethereum, 0xce31…b89b sent about $599,714 to a wrong approximate matching address.
Expected: 0x77f6ca8E…a346
Error: 0x77f6A6F6…A346
(3) On February 18, victims from addresses starting with 0x308a signed a malicious USDT approval (approve(address,uint256)), resulting in about $337,069 in USDT being transferred to the scammer's wallet.
(4) On February 18, a victim, after copying a contaminated transaction history, sent $157,000 to a similar address.
Expected: 0xa7a9c35a…03F0 → Sent to: 0xa7A00BD2…03F0
(5) On February 25, victims from addresses starting with 0xb30 suffered a loss of $388,051 on Ethereum after signing a phishing token approval.
(6)Hardware Wallet Impersonation Verification Phishing Scam
Date: February 12
Nature of the Incident: Hackers forged an official verification page for a mainstream hardware wallet, sending "wallet security risk warnings" via email and SMS, luring users to enter their mnemonic phrases and private keys for "security verification," successfully obtaining the mnemonic phrases of multiple users and stealing assets from their accounts, with total losses of approximately $950,000.
(7) Fake DEX Address Hijacking Rug Pull
Date: February 17
Nature of the Incident: Hackers tampered with user transfer addresses and forged DEX trading interfaces, luring users into transferring to fake addresses. After users completed the transfers, they immediately consolidated the funds into multiple anonymous addresses, with total losses of approximately $600,000 USDT, affecting over 200 victims. According to monitoring, the maximum loss for a single victim in this attack was about $600,000.
(8) Fake Uniswap Official Phishing Website Scam
Date: February 19 – February 26
Nature of the Incident: Hackers purchased Google search ads, built a phishing website that closely resembled the official Uniswap interface, and through social media ads and private messages, induced users to click links and complete authorizations, using the AngelFerno wallet emptying tool to steal users' crypto assets in bulk. Some victims were deceived because the fake domain name was visually indistinguishable from the real website, with over 1000 victims in a single month and total losses of approximately $1.8 million.
Summary
In February 2026, blockchain security risks showed characteristics of frequent contract attacks and increasingly sophisticated scam techniques. Hacker attacks mainly focused on oracle manipulation, cross-chain bridge security, contract permission vulnerabilities, and code flaws, with an increase in vulnerability reuse and imitation attacks, significantly raising threats to small and medium-sized protocols.
The scam end continues to primarily use phishing authorizations, fake official websites, and Ponzi scheme exits as the main tactics, and AI impersonation pages and ad hijacking have further enhanced the concealment of scams, making it increasingly difficult for ordinary users to identify them.
The Zero Time Technology security team recommends that individual users exercise caution with authorizations, verify official addresses, and avoid unknown links and high-risk projects; project teams should enhance contract auditing, private key management, and permission isolation, and pay attention to the security of oracle and cross-chain scenarios; at the industry level, strengthen threat intelligence sharing, improve the defensive capabilities across the chain, and work together to maintain eco-security.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



