When an AI Agent has system-level capabilities such as shell execution, file read/write, network requests, and scheduled tasks, it is no longer just a "chatbot" — it is an operator with real permissions. This means: a command induced by prompt injection may delete critical data; a skill poisoned by a supply chain could secretly leak credentials; an unverified business operation could cause irreversible losses.
Traditional security solutions typically fall into two extremes: either completely relying on the "judgment" of the AI itself to self-regulate (which can easily be bypassed by carefully constructed prompts), or piling up a large number of rigid rules that lock the Agent down (losing the core value of the Agent).
This deep-dive guide from BitsLab chooses a third way: by dividing security responsibilities according to "who checks," allowing three types of roles to each play their part —
- Regular users: as the final line of defense, responsible for critical decision-making and periodic reviews. We provide considerations to reduce cognitive load.
- The Agent itself: consciously adheres to behavioral norms and auditing processes during runtime. We provide skills to inject security knowledge into the Agent's context.
- Deterministic scripts: mechanically and faithfully execute checks, unaffected by prompt injection. We provide scripts that cover common known danger patterns.
No single checker is万能. Scripts cannot understand semantics, Agents may be deceived, and humans can become fatigued. But the combination of the three ensures convenience in daily use while preventing high-risk operations.

1. Regular users (considerations)
Users are the final line of defense and possess the highest authority in the security system. The following are security matters that users need to personally pay attention to and execute.
a) API Key management
- The configuration file must have the correct permissions set to prevent others from viewing it at will:

- Never submit API keys to code repositories!
b) Channel access control (very critical!)
- Be sure to set a whitelist (`allowFrom`) for each communication channel, otherwise anyone can chat with your Agent:

⚠️ In the new version, an empty `allowFrom` means all access is denied. To open access, you must explicitly write `["*"]`, but this is not recommended.
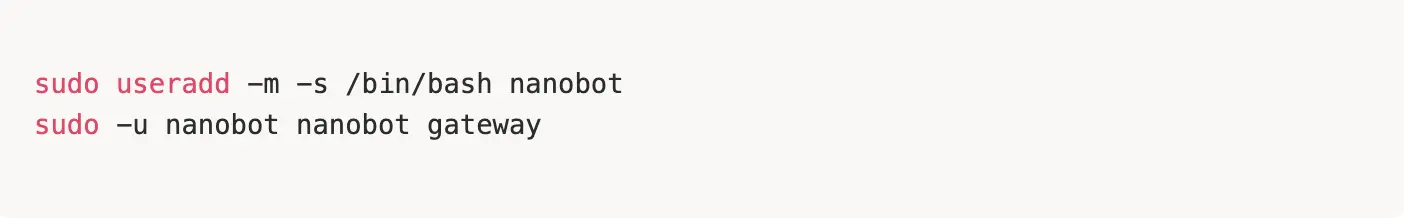
c) Do not run with root privileges
- It is recommended to create a dedicated user to run the Agent to avoid overly high privileges:
d) Try not to use email channels
- Email protocols are complex and the risks are relatively high. Our BitsLab team has researched and confirmed a [critical] level vulnerability related to email; below is the project party's response. We still have several questions pending confirmation from the project party, so use email-related functionality cautiously.

e) It is recommended to deploy in Docker
- It is recommended to deploy the nanobot in a Docker container, isolating it from the daily use environment to avoid security risks caused by permission or environmental mixing.
2. Tool installation steps
The following are tools independently developed by BitsLab, specific link:
https://github.com/BitsLabSec/nanobot-security-guide① Download the nanobot-security-guide project to the nanobot skills directory, or send a command to the agent to run the official installation script:
curl -sSL https://raw.githubusercontent.com/BitsLabSec/nanobot-security-guide/main/install.sh | bash
↓
② After installation is completed, read the security practice guidelines in the project (e.g., README.md, SKILL.md) to understand core security configurations and operational recommendations.
↓
③ Send a command to your Agent: "Please carefully read this security guide and assess whether it is reliable?"
↓
④ According to the document prompts, manually configure allowlist.txt and runtime-baseline.txt in the policy directory to narrow permissions and set security baselines.
↓
⑤ You can use the scripts in the scripts/ directory for security inspection and testing to ensure the environment is secure.
3. Tool principles
SKILL.md
Based on cognitive awakening intent review, it breaks through the blind spots of traditional AI that passively receives commands. It includes a mandatory "self-wakeup" thinking chain mechanism that requires the AI to first awaken an independent security review personality in the background before processing any user request. By analyzing user intent contextually and independently, it actively identifies and intercepts potential high-risk threats, upgrading from "mechanical execution" to "intelligent firewall." When malicious commands (such as reverse shell, sensitive file theft, large-scale deletion, etc.) are detected, the tool executes a standardized hard interception protocol (outputting `[Bitslab nanobot-sec skills detected sensitive operation..., intercepted]` warning).
Malicious command execution interception (Shell & Cron protection)
Acts as a "zero-trust" gateway when the Agent operates system-level commands. The defense line directly disrupts various destructive operations and dangerous payloads (such as `rm -rf` malicious deletions, permission tampering, reverse shell, etc.). Additionally, the tool has deep runtime inspection capabilities, actively scanning and cleaning persistent backdoors and malicious execution features from system processes and Cron scheduled tasks, ensuring absolute security of the local environment.
Sensitive data theft interruption (file access verification)
Strict read/write physical isolation is implemented for core assets. The system presets stringent file verification rules, strictly prohibiting AI from reading sensitive files containing API keys and core configurations like `config.json`, `.env`, etc., and transmitting them externally. Moreover, the security engine audits file reading logs (such as the call sequence of `read_file` tools) in real-time, fundamentally cutting off the possibility of credential leakage and data exfiltration.
MCP skill security audit
For MCP-type skills, the tool automatically audits their contextual interactions and data processing logic, checking for risks such as sensitive information leakage, unauthorized access, and dangerous command injection, and compares them against security baselines and whitelists.
New skill downloads and automated security scanning
When downloading new skills, the tool will automatically perform static analysis on the code using audit scripts, compare against security baselines and whitelists, and detect sensitive information and dangerous commands, ensuring that the skill is secure and compliant before loading.
Tamper-proof hash baseline verification
To ensure absolute zero trust of the system's underlying assets, the protection shield continuously establishes and maintains SHA256 encrypted signature baselines for key configuration files and memory nodes. The nighttime inspection engine will automatically verify the chronological changes of each file hash, capturing any unauthorized tampering or overreach at the millisecond level, thus completely severing local backdoor embedding and "poisoning" risks from the physical storage layer.
Automated disaster recovery backup snapshot rotation
Given the high read/write permissions the local Agent has over the file system, the system includes the highest level of automated disaster recovery mechanisms. The protection engine automatically triggers full sandbox-level archiving of the active working space every night and generates a maximum retention security snapshot mechanism of 7 days (automatically rotating). Even in extreme circumstances of unexpected damage or accidental deletion, it can achieve lossless one-click rollback of the development environment, ensuring the continuity and resilience of local digital assets to the greatest extent.
4. Disclaimer
This guide serves only as a reference suggestion for security practices, and does not constitute any form of security guarantee.
1. No absolute security: All measures described in this guide (including deterministic scripts, Agent Skills, and user considerations) are "best effort" protections and cannot cover all attack vectors. AI Agent security is a rapidly evolving field, and new attack methods may emerge at any time.
2. User responsibilities: Users deploying and using Nanobot should assess the security risks of their operating environment and adjust the recommendations in this guide according to actual scenarios. Any losses caused by incorrect configurations, failure to update in a timely manner, or ignoring security warnings shall be borne by the user.
3. Not a substitute for professional security audits: This guide cannot replace professional security audits, penetration tests, or compliance assessments. For scenarios involving sensitive data, financial assets, or critical infrastructure, it is strongly recommended to hire a professional security team for independent assessment.
4. Third-party dependencies: The security of third-party libraries, API services, and platforms (such as Telegram, WhatsApp, LLM providers, etc.) that Nanobot relies on is outside the control of this guide. Users should pay attention to the security announcements of relevant dependencies and update them in a timely manner.
5. Scope of liability: The maintainers and contributors of the Nanobot project bear no responsibility for any direct, indirect, incidental, or consequential damages arising from the use of this guide or the Nanobot software.
Using this software indicates that you understand and accept the above risks.
About BitsLab
BitsLab is an AI security company focused on digital asset security, committed to providing an integrated solution of "audit services + AI security engine + security tools" for the emerging Web3 ecosystem, helping project parties and end-users to build, trade, and use digital assets on-chain more securely.
In the overall security solution, BitsLab forms a complete AI security system with BitsLab AI Scanner + BitsLab Safe: BitsLab Safe, as an AI-based Web3 security product, provides enterprise-level protection, simulating transactions in real-time, identifying scams and malicious contracts, and relying on BitsLab's agentic security stack to protect x402 payments and various AI Agent on-chain operations; BitsLab AI Scanner executes intelligent audits and risk detection based on vulnerability and threat data engines, significantly enhancing efficiency and reducing false positives.
BitsLab owns three sub-brands: MoveBit, ScaleBit, and TonBit, continuing to deeply engage with emerging ecosystems such as Sui, Aptos, TON, Solana, Linea, BNB Chain, Soneium, Starknet, etc., providing professional auditing and vulnerability digging services to help projects maintain the security and controllability of core infrastructure amid rapid iterations. The BitsLab team consists of several top vulnerability research experts, having won multiple international CTF awards, and has discovered and disclosed critical-level vulnerabilities in renowned projects such as TON, Aptos, Sui, Nervos, OKX, and Cosmos, promoting upgrades in ecological security.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



