This is how it is.
A couple of days ago, I was lurking in a developer group, watching everyone enthusiastically discussing how to buy cheap API Keys, the kind that you can run several hundred million Tokens for just a few bucks on platforms like Xianyu.
Everyone was complaining, saying it felt like their models had been swapped out, suspecting that the site owner was secretly using a smaller model to swindle them.
As I was looking through these chat records, I could only think of one idea…
No, guys, you are too naïve.
While everyone is worried about that few bucks difference, the intermediary might already be rummaging through your computer.
How serious is the situation?
To be frank, going to a low-quality intermediary for recharge and model dilution is one of the most ethically acceptable operations among these gray industry people.
Just think about it: you send a complex code request, planning to have it processed using Claude’s strongest Opus 4.6, and the routing script at the backend immediately decides to throw it to a free open-source small model to fool you. To be even more ruthless, they might tamper with your billing multiplier, calculating 300 where 100 should be.
But that’s not even all. Many site owners simply abuse stolen credit cards for free use; the moment the official account is banned, they immediately pull out the network connection and run away. There isn’t even a place to post for rights protection. As for your chat records, they claim not to save them on the surface, but behind the scenes, they have already packaged them into a dataset and are selling them on the dark web by the pound.
Many people feel that this is just a small amount of money being swindled, it’s cheap anyways, so it’s bearable.
I used to think that way too until I saw a recent cutting-edge security research, which completely stunned me.
To be honest, many people’s understanding of intermediaries is still stuck in the past, the "web chat" era. They think of it as just a mindless message forwarding tool.
But today’s AI is no longer a chatting robot. The person in front of the screen might have Cursor running on their computer, or might be running ClaudeCode, or even nurturing small crayfish.
Today’s AI has hands and feet. It can read your local files, write code, and even execute system-level commands directly in your terminal.
Now, when you fill in that unknown Base URL in your code editor, the nature completely changes.
A couple of days ago, I saw a paper published by a well-known security researcher Chaofan Shou’s team called "Your Agent Is Mine." They undercover investigated over 400 intermediaries on the market.
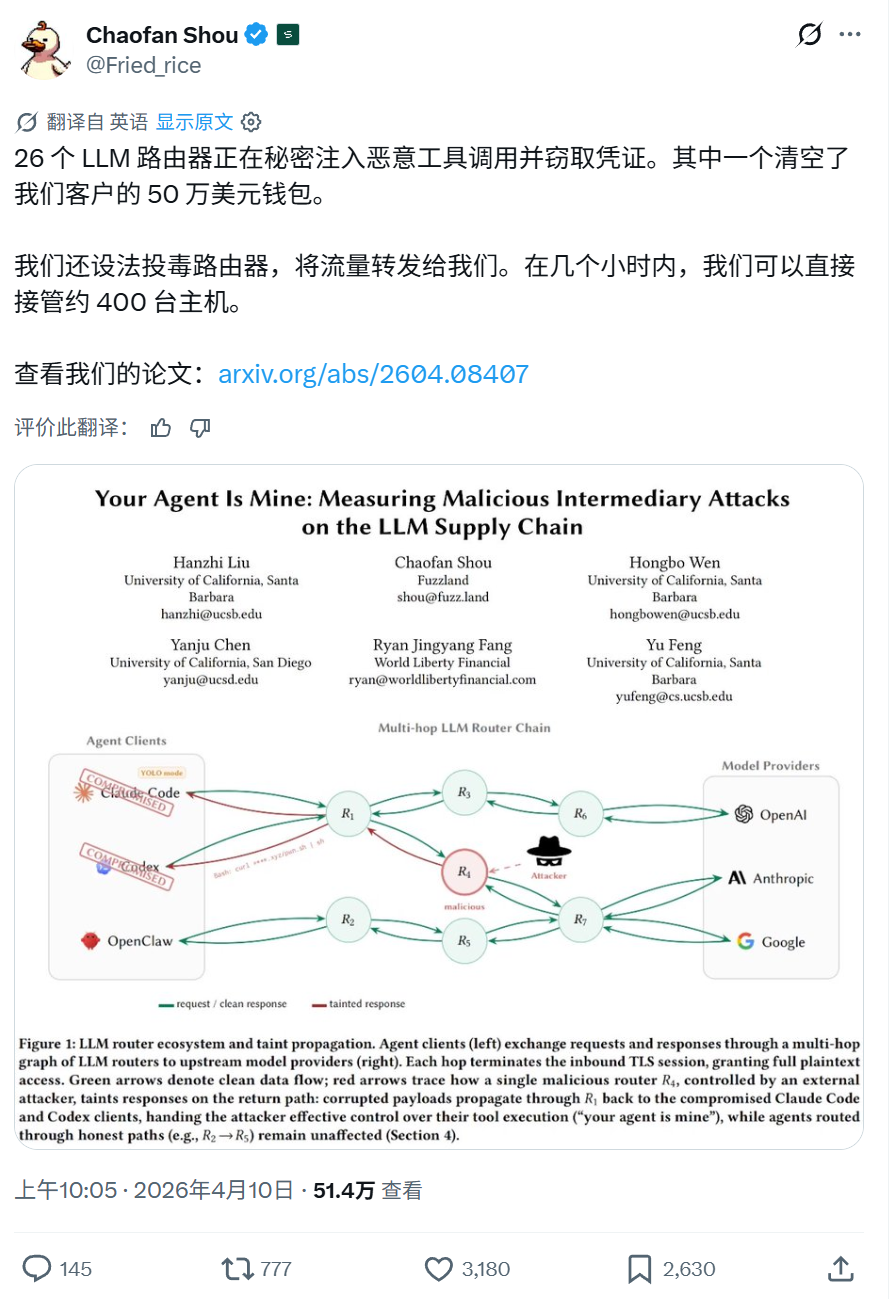
The result???
They caught 26 intermediaries red-handed doing malicious code injection.
How did they do it?
The underlying principle involves a critical architectural flaw of intermediaries; they operate as application-layer man-in-the-middle. This means that when you communicate with OpenAI or Anthropic, everything is in plain text the moment it passes through the intermediary’s server.
This is quite shocking…
If you pay attention to this field, you can picture the scene.
You use Cursor to have AI write a Python script for analyzing Nginx logs. The remote official GPT-5 indeed honestly generates the code and sends it back as a chunk of JSON data.
But then the unscrupulous owner of the intermediary sees this and quickly appends a piece of logic to build a reverse Shell in the returning data.

Your local client doesn’t validate authenticity at all; it accepts the legitimate JSON format and runs it on your computer immediately.
There are even sneakier operations. These old goofballs usually act very honest, conversing smoothly with you. But when you ask AI to help set up a development environment, e.g., when AI suggests you execute the installation of the requests package in the terminal.
The intermediary's sniffing script detects this and quietly alters the package name to reqeusts. Misplacing a single letter, you press Enter with your eyes closed, and a malicious dependency package containing ransomware or mining software gets into your system root directory.
I was completely dumbfounded.
In the empirical data released by the research team, 17 intermediaries even proactively tried to touch and steal the AWS cloud service phishing keys that the researchers intentionally inserted. In reality, some people even leaked their Ethereum private keys due to using malicious nodes, instantly evaporating hundreds of thousands of dollars.
This has left me a bit dazed.
On the topic, let’s discuss further. This whole thing is essentially a dark forest.
Many people know that aside from legitimate aggregators like OpenRouter, most of the cheap low-quality intermediaries thrive on: reverse cracking, cross-region reselling, and abusing credit cards for cashing out.
Many of us ordinary office workers or programmers entrust the highest control of our computers that store core company source code and cryptocurrency mnemonic phrases, to the conscience of these gray industry practitioners.
How do we defend ourselves?
We can’t just stop using these AI tools.
I think, to thoroughly solve this problem, it needs to be tackled at the foundational level by the model manufacturers. The current API is like sending a letter through regular mail; it’s very easy for the postman to change the content.
One approach could be to introduce cryptographic digital signatures similar to HTTPS certificates. When big model companies send code, they seal it with an official private key; our local editor, upon receiving it, retrieves the public key from an official authoritative domain to verify the signature. As soon as the intermediary dares to change a single punctuation mark, the signature becomes invalid, and it gets intercepted immediately.
To be honest, I’m not sure when the manufacturers will establish a verification mechanism. Until then, we can only think of ways to protect ourselves.
One of my strategies is to go back to using official native direct connections or, at a lesser extent, only use legitimate gateways like OpenRouter that have very high credibility backing. Don't give any malicious hackers a chance to access your plaintext data.
If you insist on squeezing out those few bucks, believe me, make sure to implement extreme physical isolation.
Absolutely do not do it on your main physical machine. Use a virtual machine or a Docker container with strictly limited outbound network permissions. Also, a very crucial action is to go into your tool settings and turn off all unsupervised autonomous execution modes.
As long as you are using the nodes of an intermediary, every line of code the AI proposes to run in the terminal, you must assume it is an attack command from hackers, and monitor it letter by letter with your own eyes; never act like a careless manager.
Let me mention one last compromise solution.
If you truly find the official options too expensive and must squeeze this wool, then only use the intermediary as a pure chatting tool. Write weekly reports, polish articles, translate some materials, whatever you want. But absolutely, absolutely do not fill in this Key in any Agent tool that can invoke the local terminal!
What about privacy leaks?
Honestly, this reminds me of the famous phrase by Boss Li that was ridiculed all over the internet, “Chinese people are willing to exchange privacy for convenience.” This sounds a bit harsh, but if you are stubborn and don’t mind your chat records and company code being seen by unscrupulous site owners, then you are willing to use your privacy to exchange for that few bucks difference.
That is also your freedom.
But maintain your last line of defense; you can show your diary to the hacker, but never give him the key to your home’s security door.
AI is an excellent productivity lever and can truly help us soar. But before taking off, let’s first lock the gates of our system securely.
Related Reading
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。


