Just last week, the Google Quantum AI team published a groundbreaking paper indicating that under superconducting architectures, specific error correction, and hardware assumptions, future quantum computers could potentially crack the widely adopted 256-bit elliptic curve cryptography (ECDLP-256) used in current cryptocurrencies and blockchain within minutes, utilizing fewer than 500,000 physical qubits—reducing the previously estimated qubit requirement by about 20 times.
This directly points to the core ECDSA signature scheme of almost all mainstream public chains like Bitcoin and Ethereum. Once the news broke, the phrase "quantum computers can crack Bitcoin private keys" began to spread rapidly across the internet.
In fact, it is necessary to remain calm and clarify this issue—while the threat is real, it is still far from the idea that "your wallet will be insecure tomorrow."
More importantly, the entire industry has long begun to take action.
1. What exactly is quantum computing threatening?
To understand this issue, we should start from the basics: how are your crypto assets actually protected?
As we know, on Bitcoin or Ethereum, each account has a pair of keys: a private key and a public key. The private key is a string of randomly generated large numbers, extremely confidential, similar to your safe's password; the public key is derived from the private key through elliptic curve multiplication, and your wallet address is a string obtained by hashing the public key.
The security of this system is fundamentally based on the fact that this process is one-way.
In essence, it is easy to compute the public key from the private key, but deriving the private key from the public key on traditional computers requires far more time than the age of the universe. This is the essence of the "Elliptic Curve Discrete Logarithm Problem" (ECDLP)—forward computation is simple, but reverse engineering is impossible.
However, quantum computers break this assumption; they can solve integer factorization and discrete logarithm problems in polynomial time. In other words, a sufficiently powerful quantum computer could theoretically derive your private key from your public key.
So, when does the public key get exposed?
Every time you initiate a transaction on the blockchain, you need to sign the transaction data with your private key while broadcasting your public key for verification. This means that as long as you have sent a transaction, your public key has already been made public on the chain.
The significance of Google's paper lies in pushing the concept of "cracking the private key from the public key" from a theoretically feasible but absurd idea into a target that can be planned within the quantum hardware roadmap. For example, the paper estimates that cracking the 256-bit ECDLP will require about 500,000 physical qubits in a fault-tolerant quantum computer, a significant reduction from previous estimates.
Ultimately, quantum computing is not about cracking the blockchain; it primarily targets the signature systems built on the elliptic curve discrete logarithm problem within the blockchain.
Therefore, the threat is real; however, strictly speaking, the term "imminent" is not accurate. Industry consensus estimates suggest that the window period for this is still around 2030 (for further reading, see "Native Account Abstraction + Quantum Threat Resistance: Why EIP-8141 Has Not Become the Flagship of Ethereum Hegotá?").
2. What preparations are being made by various public chains?
Of course, objectively speaking, there is a key difference that many reports have not clarified: many Bitcoin addresses do not expose their public keys directly on the chain at the outset.
Take common formats like P2PKH and P2WPKH, for example; the address itself is usually just a hash of the public key, and the public key is often exposed only when it is "first spent." This means if your address has never sent a transaction, only your wallet address is on the chain, and the public key is not available.
Therefore, the most direct attack surface of quantum computing leans more towards the public keys of addresses that have already sent transactions. Of course, this detail leads directly to the first thing users can do now, which we will discuss shortly.
The industry is not unaware of this issue. In fact, preparations for post-quantum cryptographic migration have already been advancing on multiple fronts.
The response strategy of Ethereum is to decouple the account layer from the signature scheme. For instance, the progression of EIP-7702 and account abstraction (AA) allows Ethereum accounts to define what constitutes a valid signature through smart contract logic. This means that someday in the future, when post-quantum signature schemes are introduced, it will not be necessary to rewrite the underlying protocol, only to replace the signature verification module of the account.
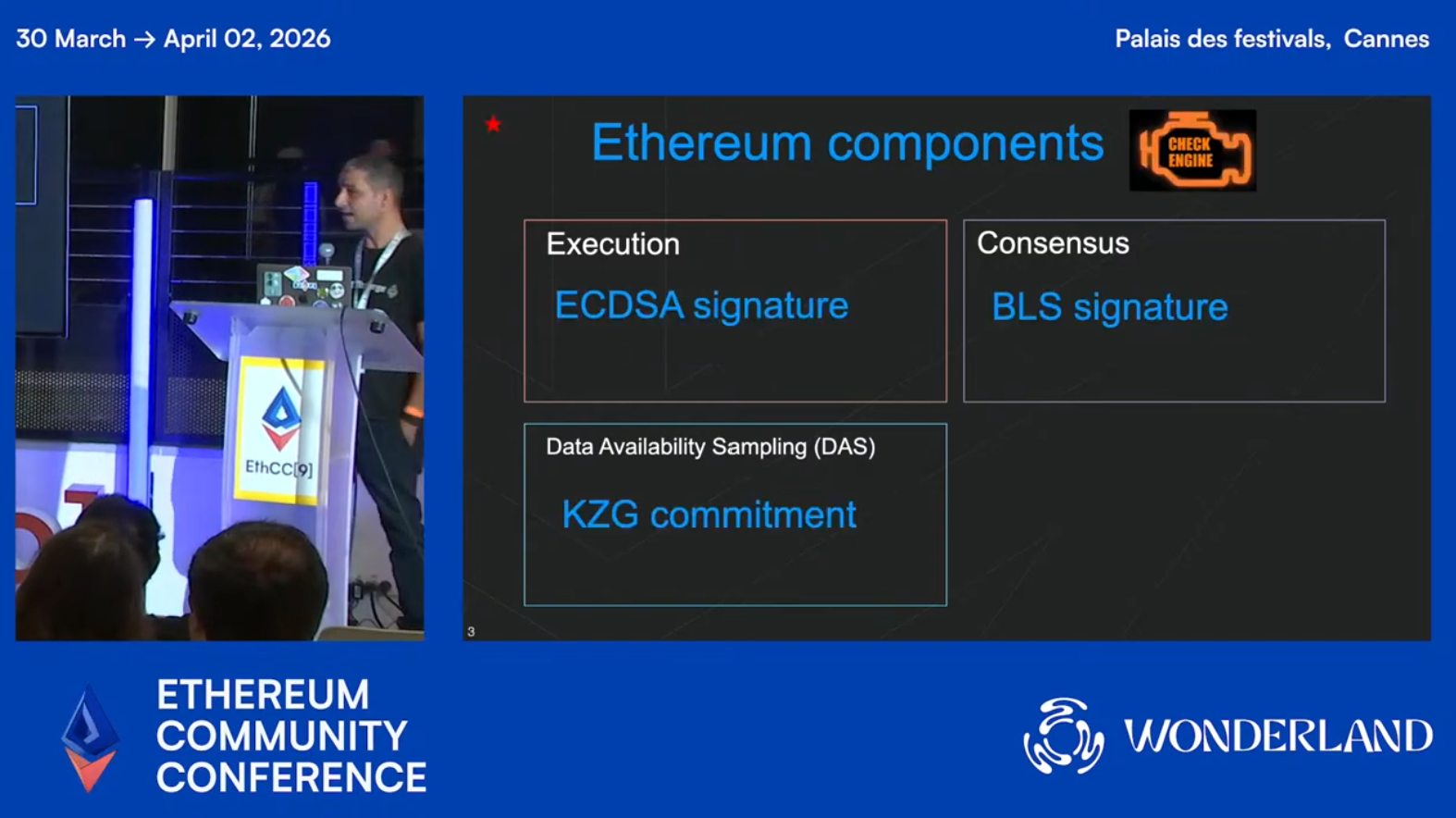
Furthermore, Ethereum Foundation cryptography researcher Antonio Sanso updated the latest progress on Ethereum's quantum resistance at the EthCC9 conference, noting that quantum computers might pose a real threat to the ECDSA signature algorithm by the mid-2030s. Ethereum has currently completed about 20% of its post-quantum preparation work and plans to achieve full quantum resistance through the Lean Ethereum upgrade between 2028 and 2032.
However, the main technical challenge currently faced is the size of the signature. For example, the size of the signature for the lightest post-quantum signature algorithm, Falcon, is still more than ten times that of ECDSA, making direct verification of lattice-based signatures in Solidity extremely costly in gas. Consequently, the research team has established two core technical paths:
- First, to allow users to upgrade their wallet signature algorithms to post-quantum schemes via account abstraction, without needing to modify the underlying protocol;
- Second, to introduce LeanVM to handle complex hash computations and integrate zero-knowledge proofs to verify the ownership of address mnemonic words, ensuring asset security during the migration process;
Antonio stated that he will chair biweekly ACD meetings on post-quantum topics starting in February 2026. Currently, consensus clients like Lighthouse and Grandine have launched experimental post-quantum testnets.
In addition, the Bitcoin community's style is notably more conservative. The recently added BIP360 in the BIPs repository proposes a new output type, P2MR (Pay-to-Merkle-Root), one of its design goals is to eliminate the quantum-vulnerable key-path spending in Taproot and to leave a more friendly structure for potential future post-quantum signature migration.
Of course, a proposal entering the BIPs repository does not mean it has formed community consensus, nor does it mean it will soon be adopted. Therefore, it can only be said that discussions within the Bitcoin community regarding quantum exposure and potential output type changes have begun, which aligns with Bitcoin's consistent style of first clearly defining issues before very slowly forming consensus.
It is worth noting that as early as 2024, the National Institute of Standards and Technology (NIST) officially released three post-quantum cryptography standards, indicating that the blockchain ecosystem now has clear migration targets and no longer needs to wait for discussions on which algorithm is better to converge; the engineering implementation has effectively already begun.
3. What should ordinary users do?
Although the threat of quantum computers is years away, that does not mean we should ignore it now; some good habits formed today come at almost no cost.
The first is to avoid address reuse, which is the most direct and effective self-protection measure.
The reason is as mentioned above—if you are a user of UTXO chains like Bitcoin, every time you initiate a transaction, your public key will be exposed on the chain. If you always use the same address, the public key is continually made public. Once quantum computing power matures, attackers can easily reverse-engineer your private key from your public key.
Currently, mainstream wallets like imToken already provide HD wallet functionality by default. A good habit would be to use a new address for each transfer and not treat a single address as a permanent identifier for repeated use. For those addresses that have never sent transactions, the public key has never been exposed, so the current quantum threat is almost not applicable.
Next, pay attention to the post-quantum upgrade paths of wallets.
If you primarily use account model chains like Ethereum, the focus is not on mechanically switching to new addresses but on whether your wallet and the public chain you are on will provide a clear migration path in the future.
For account model chains, the bigger issue in the quantum era is often not the one-time exposure but the long-term binding of active accounts, public key history, on-chain identity, and application permissions. When the actual migration window arises in the future, the accounts that are more upgradeable and the wallets that can replace signature logic more smoothly will be safer.
Lastly, from a human perspective, it can be foreseen that with the rising popularity of the topic, there will be more wallets or protocols claiming "quantum security" on the market. We should remain cautious of these wallets, protocols, and infrastructure products that tout "quantum security."
In the face of such claims, the most critical questions to ask are not promotional materials but three tougher ones:
- Is the algorithm it relies on a finalized standard from NIST?
- Has its security undergone independent audits and sufficient implementation verification?
- Is the quantum security it claims related to chain-level migration, account-level upgrades, or merely application-layer packaging?
After all, true post-quantum security ultimately needs to cover not just a single app's label but the entire path from signature, verification, to on-chain compatibility.
Overall, the threat of quantum computing to blockchain is real. The importance of Google's latest white paper is indeed in pushing this threat closer from a distant theory to a manageable risk.
However, this still does not signal that "your wallet will be hacked tomorrow." A more accurate understanding should be that post-quantum migration is no longer a topic that belongs solely to the academic sphere but will gradually enter realistic issues of protocol upgrades, wallet designs, and user asset management in the coming years.
In Conclusion
For the industry, what is truly important next is not who first shouts that quantum is coming, but who can first clearly design the migration path.
For users, it is not about panicking right now but establishing a basic recognition of risks: which assets are exposed first, which actions will amplify exposure, and which wallets and public chains are more likely to provide smooth upgrades in the future.
What we need is to act early, not to become overly anxious.
Let’s encourage each other.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



