Original author: Nicky, Foresight News
Recently, Drift Protocol released the latest investigation results of the attack incident, indicating that the operation was carried out by the same threat actor as the October 2024 Radiant Capital hacker incident, with highly consistent on-chain capital flows and operational methods. Security company Mandiant attributed the Radiant Capital attack to UNC4736, a group linked to the North Korean government.
After the Drift attack incident, the hackers have accumulated 130,293 ETH, worth about $266 million. The incident affected 20 protocols, including Prime Numbers Fi, Gauntlet, Elemental DeFi, Project 0, among others. Prime Numbers Fi estimated losses of over $10 million, Gauntlet approximately $6.4 million, Neutral Trade about $3.67 million, Elemental DeFi around $2.9 million, and Elemental expressed hope to obtain some compensation from Drift.
Drift stated in a declaration that this attack was a carefully planned operation lasting six months. In the fall of 2025, a group claiming to be a quantitative trading company approached Drift contributors during a large cryptocurrency conference. Based on the timeline, notable large cryptocurrency conferences during this period include Korea Blockchain Week 2025 (September 22 to 28, 2025, held in Seoul), TOKEN2049 Singapore (October 1 to 2, 2025, held in Singapore), Binance Blockchain Week Dubai 2025 (October 30 to 31, 2025, held in Dubai), Solana Breakpoint Dubai (November 20 to 21, 2025, held in Dubai), etc.
Drift officials stated that they were skilled, had verifiable professional backgrounds, and were very familiar with the operational methods of Drift. The two parties established a Telegram group, and over the following months, substantial discussions centered around trading strategies and treasury integration took place.
From December 2025 to January 2026, this group officially settled in an ecological treasury on Drift, filling out strategy detail forms as required. They had multiple working discussions with several contributors, raising detailed product issues and deposited over $1 million of their own funds. Through patient and orderly operations, they established a fully functional business presence within the Drift ecosystem.
Integration discussions continued until March of this year. Several Drift contributors met these individuals face-to-face again at multiple international conferences. By this time, the two sides had established nearly six months of cooperative relationships, and the counterpart was no longer a stranger but a partner they had worked with. During this period, the counterpart shared links to the projects, tools, and applications they claimed to be building, which is a routine practice among trading companies.
After the attack on April 2, investigators conducted a comprehensive forensic review of known affected devices, accounts, and communication records, with interactions with this trading team becoming the most likely infiltration path. At the time of the attack, the counterpart's Telegram chat logs and malware had been thoroughly cleared.
The investigation showed that the attackers may have infiltrated the devices of Drift contributors in three ways. One contributor might have been compromised after cloning the code repository shared by the team, which was disguised as a front end for deploying their treasury. Another contributor was induced to download a TestFlight app, which the counterpart claimed was their wallet product. Regarding the infiltration path targeting the code repository, the security community had previously warned several times between December 2025 and February 2026 of known vulnerabilities in VSCode and Cursor, where simply opening a file, folder, or repository in the editor could silently execute arbitrary code without any user clicks or prompts. A complete forensic analysis of the affected hardware is still ongoing.
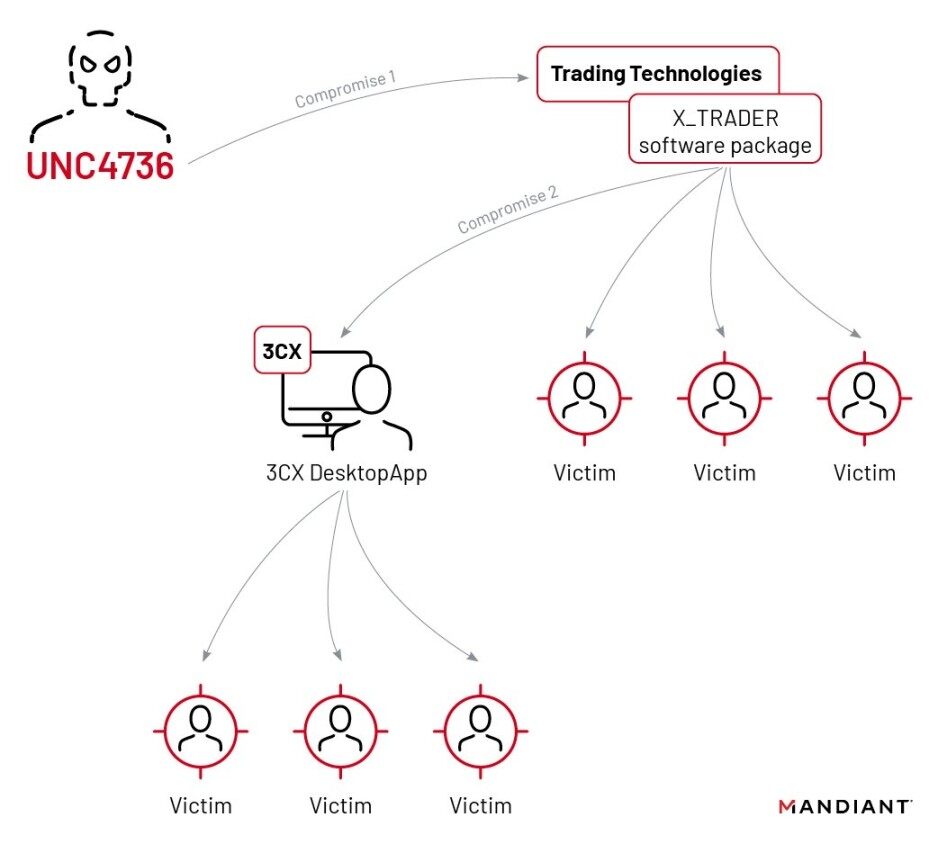
This operation is from the same threat actor involved in the October 2024 Radiant Capital hacking incident. Mandiant attributed the Radiant attack to UNC4736, a North Korean state-sponsored organization also known as AppleJeus or Citrine Sleet. The attribution is based on two aspects: on-chain fund flows show that the funds used to plan and test this operation can be traced back to the Radiant attackers; operationally, the identities used in this action have recognizable overlaps with known North Korean-associated activities.
Drift pointed out that the individuals appearing in offline meetings were not of North Korean nationality. High-level North Korean threat actors typically establish face-to-face relationships through third-party intermediaries.
UNC4736 is a cluster of threat actors tracked by Mandiant, with a high confidence assessment that it belongs to North Korea's Reconnaissance General Bureau. This organization has continuously targeted the cryptocurrency and fintech industries since 2018, stealing digital assets through supply chain attacks, social engineering, and malware delivery.
Its known major attack incidents include the 2023 3CX supply chain attack, the approximately $50 million theft from Radiant Capital in 2024, and the approximately $285 million stolen in this Drift incident. Based on statistical data, the organization has stolen a total of around $335 million.
The cluster is widely regarded as a subset of the Lazarus Group, focusing on financially motivated cybercrime. The Lazarus Group stole approximately $1.5 billion in assets from Bybit in February 2025, marking the largest theft in cryptocurrency history.
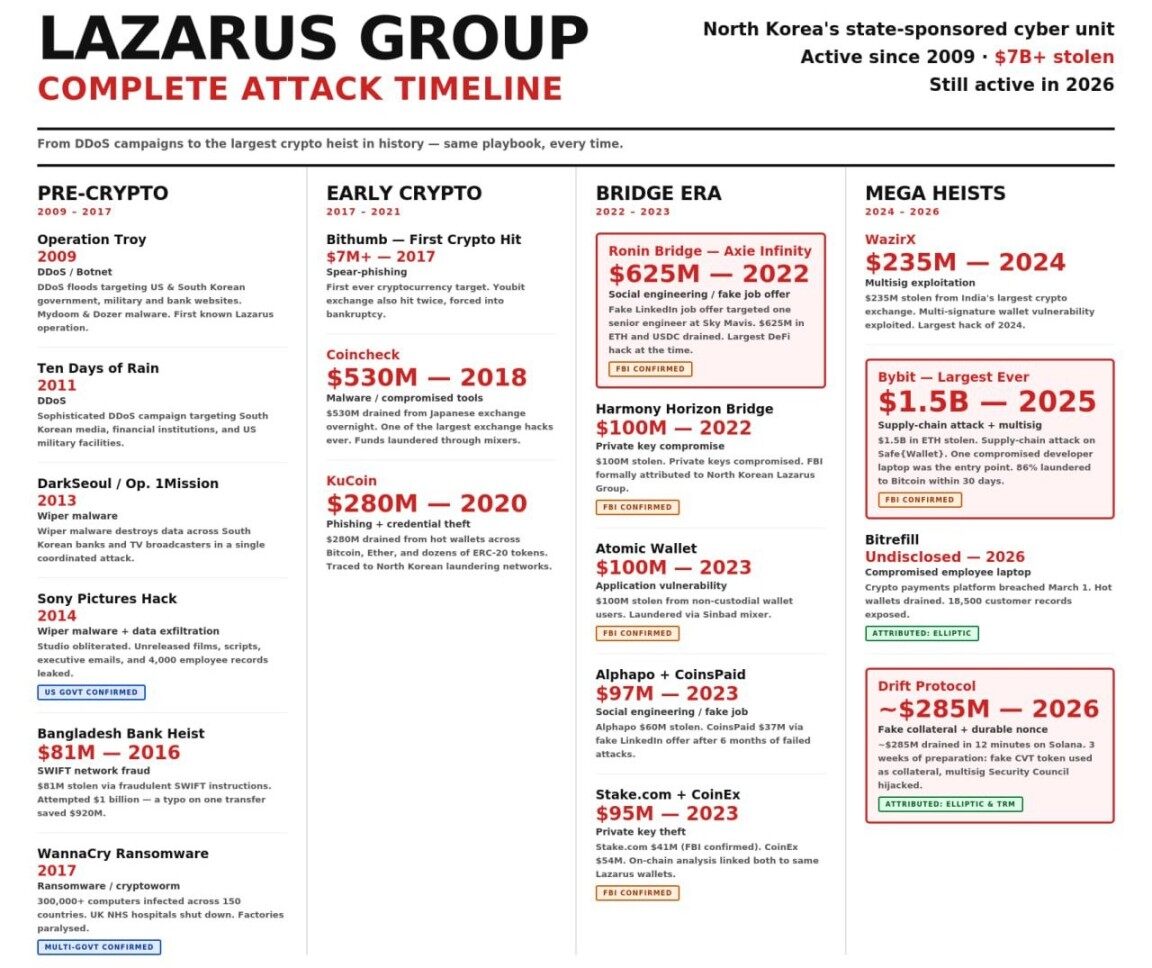
Image source: SotaMedia
The Lazarus Group is a cluster of cyber threat actors supported by the North Korean government, belonging to the Reconnaissance General Bureau, and includes various sub-clusters such as UNC4736 (i.e., AppleJeus/Citrine Sleet), TraderTraitor, etc. According to Chainalysis, North Korean hackers have cumulatively stolen approximately $6.75 billion in cryptocurrency through clusters like Lazarus, with over $2 billion stolen just in 2025.
This organization has been responsible for numerous globally sensational attack incidents: in 2014, Sony Pictures Entertainment was compromised; in 2016, the Bangladesh Central Bank was robbed of $81 million; in 2017, the WannaCry ransomware spread globally; in 2022, Ronin Bridge and Harmony Horizon Bridge were stolen from $620 million and $100 million, respectively; in 2023, Atomic Wallet and Stake were successively attacked. In October 2024, UNC4736 attacked Radiant Capital, stealing $50 million; in February 2025, TraderTraitor stole a record $1.5 billion from Bybit; in April 2026, they completed a $285 million attack on Drift Protocol.
Lazarus has cumulatively driven the total amount of cryptocurrency theft by North Korea to $6.75 billion. Attack methods have shifted from early sabotage to long-term infiltration, social engineering, supply chain attacks, and malicious smart contract/multi-signature infiltrations.
Drift's statement indicated that the investigation showed the identities used in targeted actions by third parties had complete personal and professional backgrounds, including work experiences, public qualifications, and professional networks. Those individuals seen by Drift contributors in offline meetings spent months building identity profiles that could withstand commercial cooperation background checks.
Security researcher Taylor Monahan previously stated that North Korean IT workers have been infiltrating cryptocurrency companies and DeFi projects for at least seven years, with over 40 DeFi platforms having North Korean IT worker involvement at various stages. The Drift incident further indicates that the attackers have evolved from remote job infiltrations to face-to-face targeted intelligence operations lasting several months.
Drift stated that they will continue to cooperate with law enforcement agencies, forensic partners, and the ecosystem team, with more details to be released after the investigation is completed. All remaining protocol functionalities have been frozen, the stolen wallets have been removed from multi-signatures, and the attackers' addresses have been marked at various exchanges and cross-chain bridge operators.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



