Drift Protocol, the largest decentralized perpetual futures exchange on the Solana network, confirmed the exploit after watching its total value locked (TVL) collapse from roughly $550 million to under $250 million in a single morning, now standing at $232 million. Bitcoin.com News was the first to report on the issue. The DRIFT token dropped as much as 45% in the hours that followed, bottoming near $0.04 to $0.05.
Reports note that the attack began not with a code bug but with a Tornado Cash withdrawal. On March 11, the attacker pulled ETH from the Ethereum-based privacy protocol and used those funds to deploy the carbonvote token, or CVT, on March 12. Blockchain analysts noted the deployment timestamp corresponded to approximately 09:00 Pyongyang time, a detail that raised immediate flags.
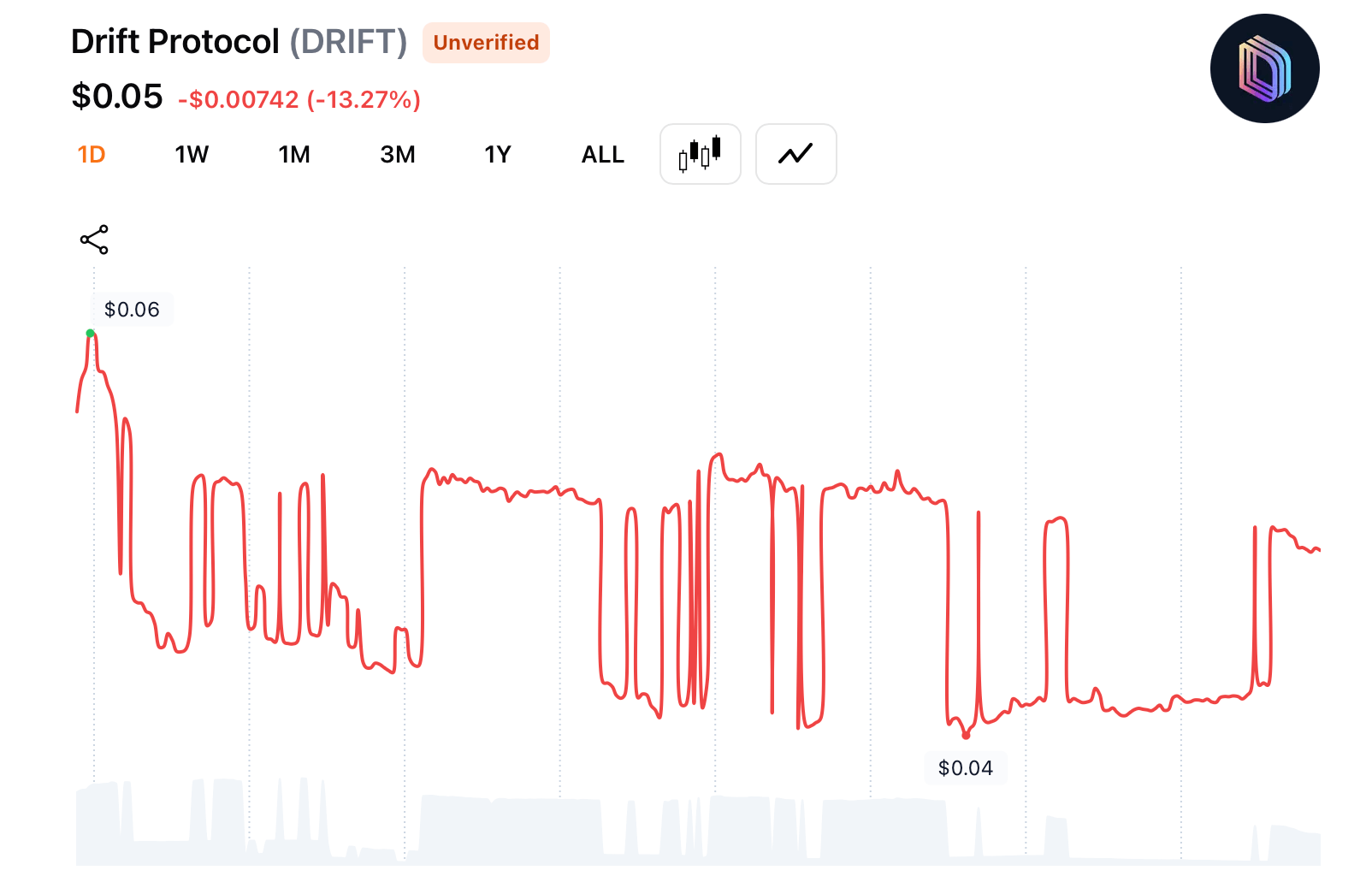
DRIFT token on April 3, 2026.
Several reports detail that over the following three weeks, the attacker seeded minimal liquidity for CVT on the Raydium decentralized exchange and used wash trading to maintain a price near $1.00. Drift’s oracles read that price as legitimate. The attacker had built fake collateral that looked real to every automated system watching it.
“Earlier today, a malicious actor gained unauthorized access to Drift Protocol through a novel attack involving durable nonces, resulting in a rapid takeover of Drift’s Security Council administrative powers,” the Drift team wrote.
The project’s X account added:
“This was a highly sophisticated operation that appears to have involved multi-week preparation and staged execution, including the use of durable nonce accounts to pre-sign transactions that delayed execution.”
Ostensibly, between March 23 and March 30, the Drift attacker moved to the human layer. Using a legitimate Solana feature called durable nonces, the attacker reportedly induced members of Drift’s Security Council multisig to pre-sign transactions that appeared routine. Those signatures became pre-approved access keys, held in reserve until the attacker was ready.
The opening closed on March 27, when Drift migrated its Security Council to a 2-of-5 signature threshold and removed its timelock entirely. A timelock typically forces a 24-to-72-hour delay on administrative actions, giving the community time to catch and reverse anything suspicious. Without it, the attacker had zero-delay execution authority. The pre-signed transactions were live the moment the timelock was gone.
On April 1, the attacker activated those transactions, listed CVT as valid collateral, raised withdrawal limits, and deposited hundreds of millions in CVT tokens against which Drift’s risk engine issued real assets. The protocol handed over millions in JLP tokens, millions in USDC, millions in SOL, and smaller amounts of wrapped bitcoin and ethereum. Thirty-one withdrawal transactions cleared in roughly 12 minutes.
The attacker converted the stolen tokens to USDC using Jupiter, bridged to Ethereum, and swapped into tens of thousands of ETH. Some funds were routed through Hyperliquid, and a portion moved directly to Binance. On April 3, Drift sent an onchain message from an Ethereum address to four hacker-controlled wallets. The message read:
“We are ready to talk.”
Security firms Elliptic and TRM Labs have attributed the attack to DPRK-linked threat actors, citing the Tornado Cash origin, the Pyongyang-time deployment signature, the social engineering focus, and the post-hack laundering speed. The Lazarus Group used the same patience and human-targeting approach in the 2022 Ronin bridge hack. The U.S. government has tied these thefts to North Korea‘s weapons program funding, and Elliptic has tracked over $300 million stolen in the first quarter of 2026 alone.
The contagion spread to more than 20 protocols. Prime Numbers Fi reported losses in the millions. Carrot Protocol paused mint and redeem functions after 50% of its TVL was affected. Pyra Protocol disabled withdrawals entirely, leaving all user funds inaccessible. Piggybank lost $106,000 and reimbursed users from its own team treasury.
DeFi Development Corp., a Nasdaq-listed company with a Solana treasury strategy, confirmed on April 1 that it had no Drift exposure. Its risk framework excluded the protocol entirely. That fact drew more attention than the company likely intended.
The Drift incident produced one clear lesson that most of the industry already knew but had not fully applied: a timelock is not optional. The removal of that single safeguard on March 27 converted a complex, multi-week attack into a 12-minute cash-out. Protocol governance without a delay mechanism is governance with an open door.
The next 48 hours following the DeFi attack were described as critical for Drift’s ability to retain user trust and map a recovery path. As of April 3, no comprehensive reimbursement plan had been announced.
- What happened to Drift Protocol? Attackers drained $286 million from Drift Protocol on April 1, 2026, using fake collateral and pre-signed administrative transactions to empty the protocol’s core vaults in 12 minutes.
- Who is responsible for the Drift Protocol hack? Security firms, including Elliptic and TRM Labs, have attributed the attack to DPRK-linked threat actors, citing laundering patterns and onchain timestamps consistent with Lazarus Group tradecraft.
- Is my money safe on Drift Protocol? Drift suspended all deposits and withdrawals following the attack; users in affected protocols like Pyra and Carrot remain unable to access funds as of April 3, 2026.
- What is a durable nonce attack in Solana DeFi? A durable nonce attack uses a legitimate Solana feature to pre-sign transactions that look routine, holding them as live authorization keys until the attacker chooses to execute them.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。



