Written by: imToken
As the Lunar New Year approaches, it is a time to bid farewell to the old and welcome the new, and also a moment for reflection:
In the past year, have you fallen into the trap of a Rug Pull project? Have you ended up "standing guard" just because of hype from a calling KOL? Or have you suffered from increasingly rampant phishing attacks, losing assets due to clicking on misleading links or signing contracts by mistake?
Objectively speaking, the Spring Festival does not create risks, but it can significantly amplify them—when the frequency of capital flow increases, when attention is distracted by holiday arrangements, and when the pace of trading accelerates, even a small mistake can be magnified into a loss.
Therefore, if you are planning to adjust your positions or organize your funds around the holiday, it's a good idea to give your wallet a "pre-festival safety check". This article will systematically outline specific actions ordinary users can take based on several real and frequent risk scenarios.
1. Beware of "AI face-swapping" and voice simulation scams
The recent popularity of SeeDance 2.0 has made everyone aware of the fact that in an era where AGI is rapidly permeating, "seeing is believing, and hearing is trusting" is becoming ineffective.
It can be said that starting from 2025, AI-based video and voice fraud technologies will become significantly advanced, including voice cloning, video face-swapping, real-time expression imitation, and tone simulation, all entering a low-threshold and scalable "industrial phase".
In fact, based on AI, it is now possible to accurately reproduce a person's voice, speech rate, pause habits, and even micro-expressions, which means that during the Spring Festival, these risks are particularly likely to be magnified.
For example, while traveling home or during a family gathering, your phone pops up a message from a "friend" in your contacts, sent via Telegram or WeChat, in an urgent tone stating that your account is restricted, needing to quickly transfer a small amount of tokens for a red envelope or temporary payment.
The voice sounds perfectly normal, and the video even shows a "real person", so how would you assess the situation while your attention is scattered by holiday arrangements?
If we were in previous years, video verification of identity was almost the most reliable method, but today, even if the other party is talking to you via a camera, it is no longer 100% trustworthy.
In this context, simply relying on watching a video or listening to a voice is no longer enough for verification. A more prudent approach would be to establish a verification mechanism with your core circle (family, partners, long-term collaborators) that is independent of online communication. This could include an offline code known only to both parties or some specific questions that cannot be inferred from public information.
Additionally, it is crucial to rethink a common pathway risk associated with links forwarded by acquaintances. After all, during the Spring Festival, backlinks titled "on-chain red envelopes" or "airdrop benefits" are easily exploited as enticing entry points for virally spreading scams in the Web3 community. Many people are not scammed by strangers, but rather trust acquaintances who forward such links and click on a well-disguised authorization page.
Therefore, it's essential to remember a simple yet extremely important principle: do not click on any unknown links directly via social platforms, and do not authorize them, even if they come from "acquaintances".
It is best to conduct all on-chain operations through official channels, saved websites, or trusted entry points, rather than completing them in chat windows.
2. Conduct an "end-of-year clean-up" of your wallet
If the first type of risk arises from trust being faked by technology, then the second type of risk comes from our own long-accumulated hidden risk exposures.
As is well known, authorization is the most fundamental mechanism in the DeFi world, yet it is often the most overlooked. When you operate in a certain DApp, you are essentially granting the contract a token management right, which could be one-time, limitless, short-term effective, or effective even after you have forgotten its existence.
Ultimately, it may not be an immediate risk point, but it constitutes a persistent risk exposure. Many users mistakenly believe that as long as assets are not stored in contracts, there are no security issues. However, during bull market cycles, people often try various new protocols, participate in airdrops, staking, mining, and on-chain interactions, leading to a continuous accumulation of authorization records. When the fever subsides, many protocols become unused, but the permissions are still retained.
Over time, these excess historical authorizations become like a heap of uncleaned keys, and if a contract vulnerability occurs in a protocol you have long forgotten about, it can easily lead to losses.
And the Spring Festival is a natural point for organization; it is worthwhile to use the relatively stable window before the holiday to systematically check your authorization records:
Specifically, you can revoke unused authorizations, especially those with unlimited permissions; apply limited authorizations for large assets you hold regularly, rather than keeping all balance permissions open for long periods; simultaneously separate long-term stored assets from those for daily operations, forming a structure with hot wallets and cold wallets.
In the past, many users needed to use external tools (such as revoke.cash and other sites) to complete these checks, but now mainstream Web3 wallets like imToken have integrated the ability to detect and revoke authorizations directly within the wallet, allowing you to view and manage historical authorizations easily.
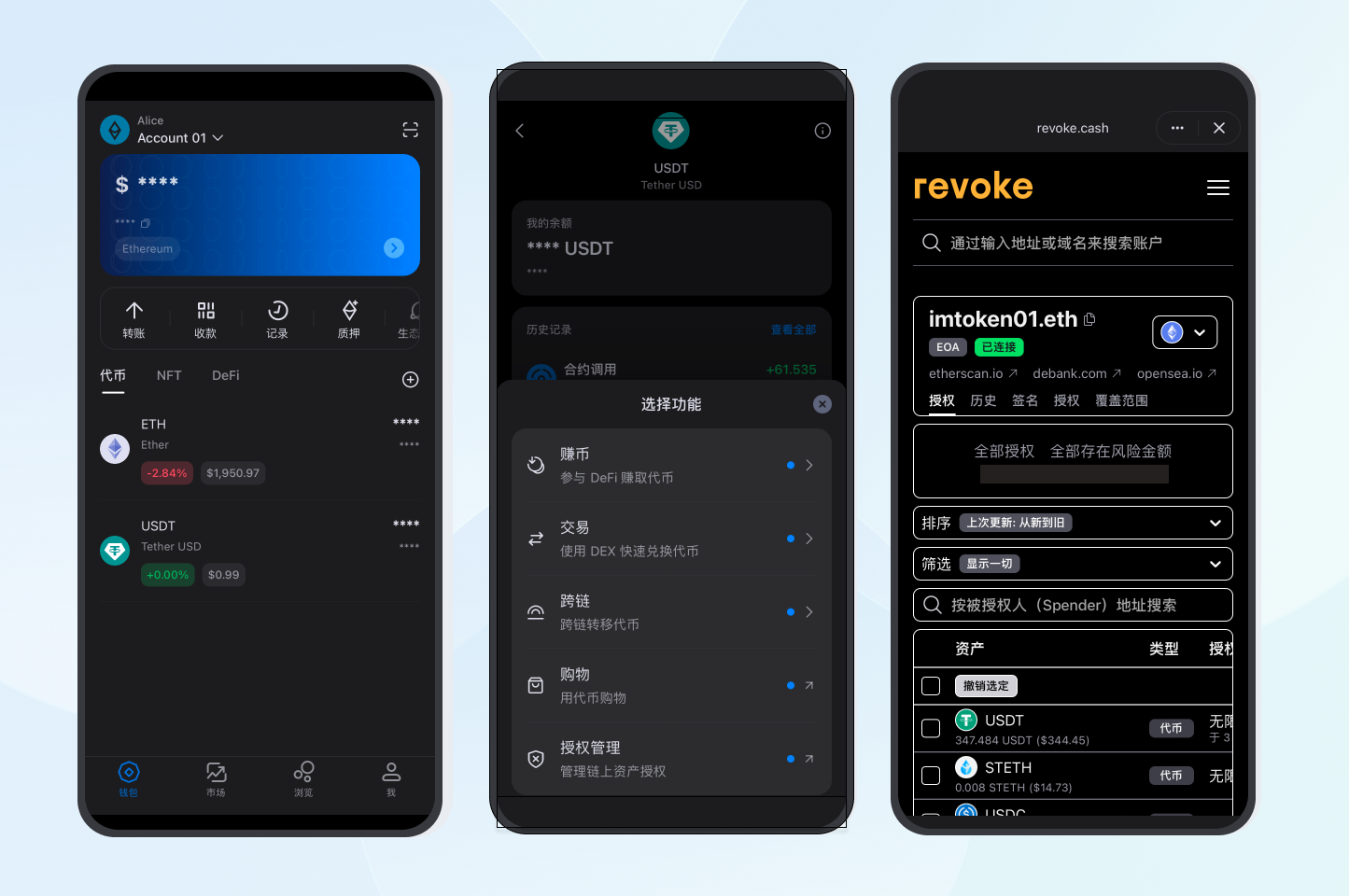
Ultimately, wallet security is not about never granting permissions but about the principle of minimal permissions—granting only the necessary permissions for the present and timely retracting them when they are no longer needed.
3. Travel, socialize, and perform daily operations without complacency
If the first two types of risks stem from technological upgrades and permission accumulation, then the third type of risk arises from environmental changes.
Traveling during the Spring Festival (returning home, traveling, visiting relatives and friends) often means frequent device switching, complex network environments, and dense social scenarios. In such environments, the vulnerabilities of private key management and daily operations can be significantly amplified.
Mnemonic phrase management is the most typical example. Saving a screenshot of your mnemonic phrase in your phone’s photo album or cloud storage, or forwarding it to yourself via instant messaging tools, is often motivated by convenience, but in a mobile context, this convenience poses the biggest hazard.
So remember, mnemonic phrases must remain physically isolated, avoiding any online storage methods; the baseline for private key security is to stay off the network.
The social context also requires boundary awareness. Showing large asset pages during holiday gatherings or discussing specific holding sizes often happens unintentionally, but it could lay the groundwork for future risks. It is even more critical to be alert to behaviors that lead to downloading disguised wallet applications or plugins under the guise of "sharing experiences" or "teaching guidance".
All wallet downloads and updates should be completed via official channels, not through social chat windows.
Additionally, before making a transfer, be sure to confirm three things: network, address, and amount. After all, there have been numerous cases of large whales mistakenly losing a significant amount of assets due to errors in similar beginning and ending number addresses, and the like phishing attacks have already been industrialized in the past six months:
Hackers often generate massive amounts of on-chain addresses with different beginning and ending numbers as a prepared seed library. Once a certain address engages in a fund transfer with the outside world, they immediately find an address with the same beginning and ending numbers from the seed library, and then invoke the contract to perform a related transfer, casting a wide net and waiting for a catch.
As some users sometimes copy target addresses directly from transaction records, only checking the first and last few digits, they fall into this trap. According to Yuxian, the founder of Slow Mist, the phishing attack targeting the first and last digits is a "net-casting attack by hackers, where willing participants will take the bait; it’s a game of probability".
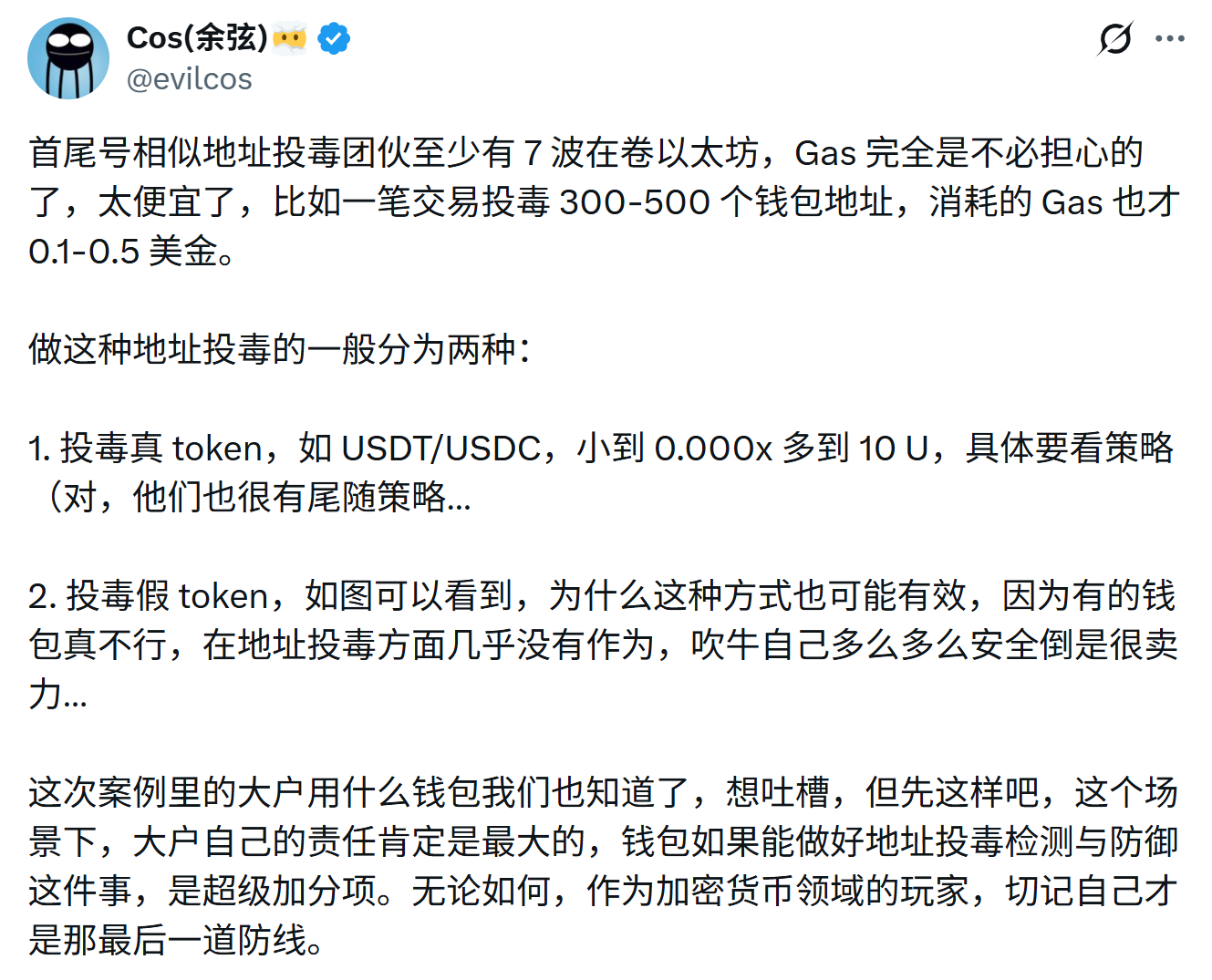
Due to the very low gas costs, attackers can poison hundreds or even thousands of addresses in bulk, waiting for a few users to make mistakes in copy-pasting. Successfully doing so even once yields far more profit than cost.
These problems don’t stem from how complex the technology is, but rather from daily operational habits:
- Check the entire address character string completely, rather than just the beginning and ending;
- Do not copy and paste the transfer address directly from the history without checks;
- When transferring to a new address for the first time, conduct a small test transfer first;
- Prioritize using the address whitelist function to fix and manage commonly used addresses;
In the current decentralized system dominated by EOA accounts, users remain their own primary responsible individuals and the last line of defense (see further reading "The 'Account Tax' of 3.35 Billion Dollars: When EOA Becomes a Systemic Cost, What Can AA Bring to Web3?").
In conclusion
Many people feel that the on-chain world is too dangerous and unfriendly to ordinary users.
To be realistic, Web3 indeed has a hard time providing a zero-risk environment, but it can turn into a manageable risk environment.
For instance, the Spring Festival is a moment when the rhythm slows down, and it is also the best time window in the year to sort out risk structures. Instead of rushing operations during the holiday, it is better to complete safety checks in advance; rather than remedying after the fact, it is better to optimize permissions and habits in advance.
I wish everyone a safe and smooth Spring Festival, and may everyone's on-chain assets remain stable and worry-free in the new year.
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




