Author: ChainUp Investment
1. Introduction
In 2025, on-chain privacy experienced a large-scale repricing event. Notably, driven by the industry’s resurgence of privacy awareness and significant advancements in cryptographic technology, Zcash saw substantial price discovery, with these technological advancements including zero-knowledge proofs (ZKPs), multiparty computation (MPC), trusted execution environments (TEE), and fully homomorphic encryption (FHE).
ZKPs: A method to prove the validity of statements without disclosing any information other than validity, enabling users to publicly share proofs of knowledge or ownership without revealing details.
MPC: A cryptographic protocol involving multiple parties collaboratively computing data by splitting it into "secret shares". No single participant sees the complete dataset.
TEE: A hardware-based solution acting as a secure "black box" within a processor, isolating data while it is being used.
FHE: A cryptographic scheme that allows computations on encrypted data without the need for decryption.
The market has shifted from "anonymity" to "confidentiality", which is a functional necessity in transparent blockchains.

In the fourth quarter of 2025, on-chain privacy attention surged, Source: Dexu
1.1. The Privacy Paradox
The history of privacy cryptocurrencies can be traced back to 2012, when Bytecoin launched CryptoNote, which offered ring signature technology later adopted by Monero in 2014. In short, privacy is not a new concept in cryptocurrency, but in the early cycle, privacy cryptocurrencies were largely an ideological pursuit or means of evasion, serving as a channel for bad actors to escape surveillance. The dilemma of on-chain privacy in previous years can be attributed to three main factors: immature technology, liquidity fragmentation, and regulatory hostility.
Historically, cryptographic technologies faced high latency and cost inefficiencies under scrutiny. Today, developer tools like Cairo (zkDSLs) and backend "surge" solutions like Halo2 enable mainstream developers to use ZKPs. The trend of building zkVM (zero-knowledge virtual machines) on standard instruction sets like RISC-V is making this technology scalable and composable across various applications. MPC is no longer just for splitting private keys; through MP-SPDZ, it supports arithmetic circuits (addition/multiplication) and boolean circuits (xor/and), allowing general computation. Advancements in GPU technology further benefit these technologies; for example, H100 and Blackwell B200 now support confidential computing, enabling AI models to operate within TEE. The greatest bottleneck of FHE, bootstrap delay (the time taken to "refresh" the noise in encrypted computations for processing to continue), has decreased from about 50 milliseconds in 2021 to less than 1 millisecond by 2025, facilitating real-time deployment of FHE-encrypted smart contracts.

Iteration and performance of zkVM, Source: Succinct, Brevis
Moreover, privacy is often isolated to specific blockchains, forcing users to leave existing active ecosystems for anonymity, incurring high transaction fees and capital opportunity costs. Today, privacy protocols like Railgun can integrate directly with DeFi applications, offering privacy as a shield against front-running and MEV extraction. Boundless, Succinct, Brevis, and similar protocols provide ZKP as a service (ZKPs-as-a-Service), while Arcium and Nillion aid in building privacy-protecting applications using MPC, and Phala and iExec compute application data within TEE without leaving their blockchain. Finally, Zama and Octra empower applications to natively handle FHE computations.

Railgun TVL, Source: DefiLlama
In earlier times, blockchains needed transparency to gain legitimacy. True builders had to distance themselves from hackers, money launderers, and other bad actors. In this environment, privacy features quickly became viewed as tools for dishonest participants. Projects like Tornado Cash, while favored by privacy-conscious users, left those users at risk of blending with the funds of illicit actors, unable to prove their innocence. This resulted in regulatory crackdowns. Exchanges froze funds from mixers in pursuit of operational licenses and delisted suspicious privacy tokens. Venture capital and institutional funds refused to hold them due to worries from compliance officers. On-chain privacy became the industry’s “criminal” feature. Today, the economic sanctions against Tornado Cash have been lifted. The industry has coalesced around the concept of "compliant privacy", allowing for the design of "viewable data" that can decrypt users' own funds' source transactions by providing audit agencies or regulatory authorities with a "view key". This approach can be seen in both Tornado Cash and Zcash.
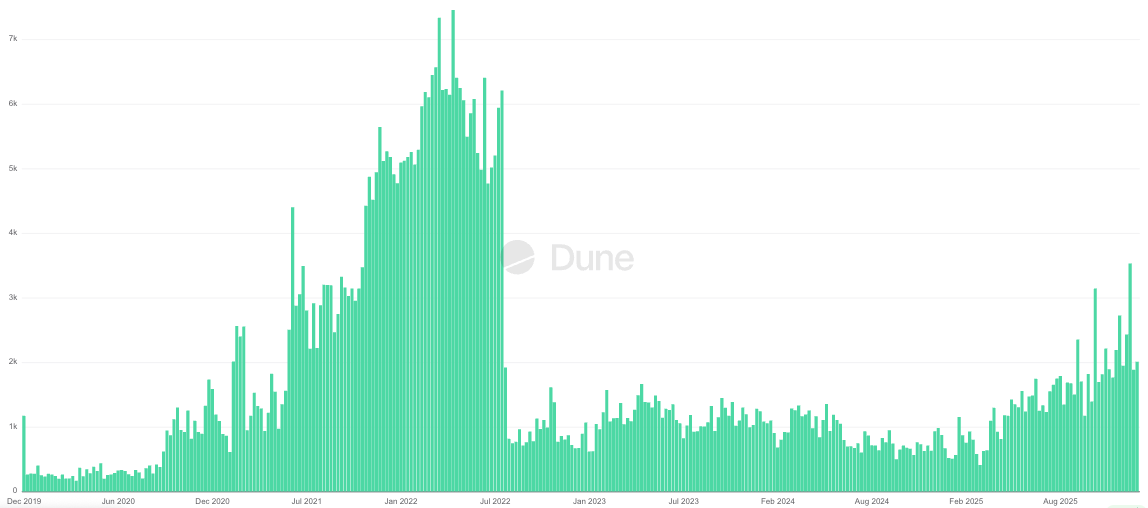
Significant impact of sanctions on Tornado Cash fund flows, Source: Dune
2. Current Privacy Technology Use Cases
The early setbacks do not mean privacy isn't important. Ask yourself a simple question: “Do you want your purchase of coffee today to expose your entire 10-year investment history?” Most people would say no, but that is exactly what the current blockchain setup does. With advancements in crypto legislation and more institutions entering the space, these new institutional participants are reevaluating the issue. Fortunately, the adoption of privacy technology in 2025 is driven more by functional utility rather than ideology.
2.1. Shielded Transactions
Utilizing a design with "viewable data", Zcash's shielded supply increased from 12% at the beginning of 2025 to approximately 29% now. The rise in demand is due to a combination of factors, such as increased speculative interest in the ZEC token and the natural desire to shield transactions from the public. The mechanism for shielded transactions is called the Commitment-Nullifier Scheme, where senders submit shielded safes to the pool, and the network uses ZKPs to validate the submitted funds to prevent double spending and create a new shielded fund safe for the receiver.
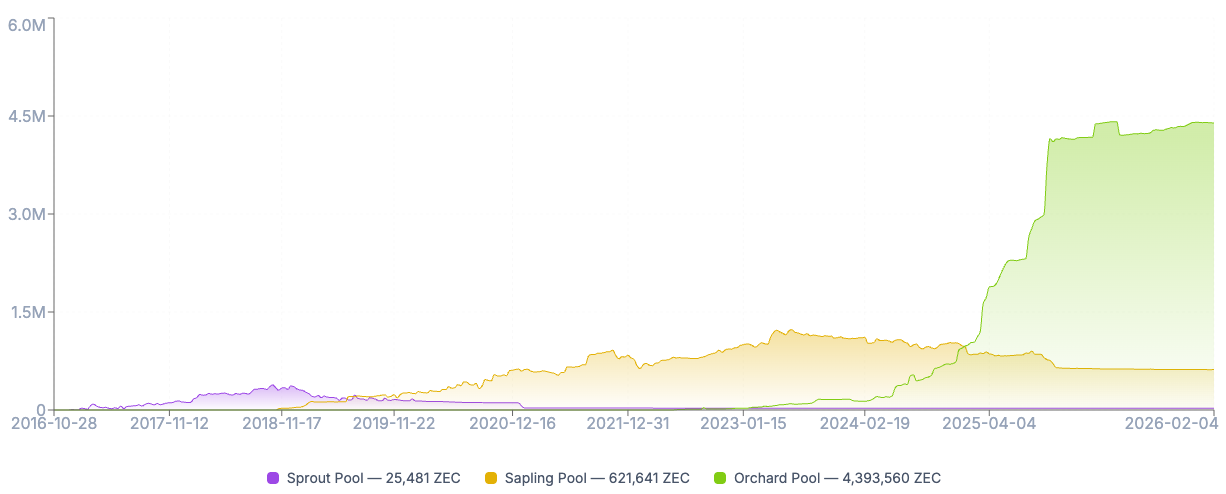
Shielding ZEC supply on Zcash, Source: ZecHub
One of the fastest-growing areas, crypto neobanks, is actively exploring implementing privacy transactions for their users, such as Fuse, Avici, and Privily. Even though some protocols use different methods to obscure on-chain transactions.
2.2. High-Performance Execution Environments
Based on total locked value (TVL), ZK layer-2 networks grew by 20% in 2025, providing significantly cheaper execution environments compared to Ethereum layer-1 networks. Layer-2 networks package all transactions on their network into a tiny data blob and send it to sorters to generate proofs and send them back to the underlying layer-1 network for validation.
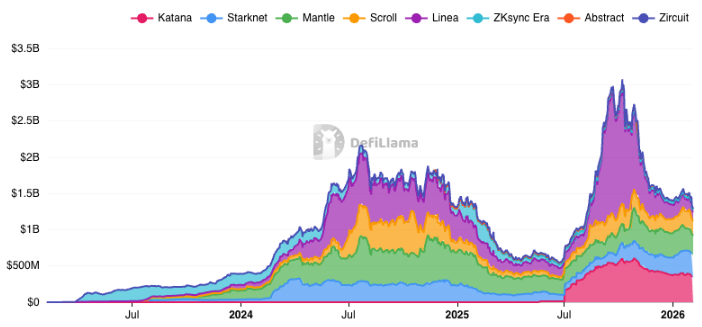
Application status of major ZK layer-2 networks: TVL trend, Source: DefiLlama
privacy smart contracts on Aztec and ZKsync Interop, which unifies liquidity between ZK chains and Ethereum.
2.3. MEV Protection
One of the most common "conceal" use cases of privacy is to prevent maximum extractable value (MEV). The transparent nature of blockchains allows predatory bots to view transactions in the public memory pool (mempool) before confirmation, enabling front-running or "sandwich" trades to extract profits. Flashbot SUAVE is decentralizing the block-building process through encrypted memory pools, where transactions remain encrypted until the block builder commits to including them. Unichain has also launched TEE-based block building to ensure transactions on the layer-two network cannot be front-run.

Percentage of transactions landed at Flashbot Protect, Source: Dune
2.4. Other Use Cases
Alongside the main use cases mentioned, developers are actively exploring implementing on-chain privacy in their applications for optimization and enhanced user experience.
Order Books: Hyperliquid's whales, such as James Wynn and Machi Big Brother, often face liquidity hunts. While Hyperliquid's founders believe transparency provides fair competitive conditions for market makers, thus leading to tighter spreads, the risk of being front-run or backtraded is a significant net negative for whale traders. This creates opportunities for Aster to offer privacy features such as hidden orders and a new shield mode planned for launch in 2026.
Identity: Certain activities, like opening new bank accounts and initial coin offerings (ICOs), require verifying the applicant's identity. Protocols like idOS allow users to upload KYC once and seamlessly reuse it across other compliant protocols, zkPass helps provide Web2 credentials to users without revealing details, World ID proves user identity through iris hashes, and ZKPassport verifies user identity without information leaving the user's device.
SEC Chair Paul Atkins stated that many types of ICOs should not be classified as securities and thus do not fall under SEC jurisdiction. His stance may lead to an increase in ICO financing in the near future, creating greater demand for crypto KYC.
Cross-Chain Bridges: Throughout blockchain history, cross-chain bridges have been easily exploited; for example, Ronin Bridge and Multichain lost $624 million and $126 million respectively due to private key leaks. ZK-cross-chain bridges minimize trust assumptions, achieving instant certainty once proofs are generated and verified, while providing scalable cost efficiency as transaction volume increases. Polyhedra Network connects more than 30 chains using zkBridge and can be inserted into the LayerZero V2 stack as "DVN".
AI: ZK can help verify outputs are generated based on expected inputs and processed by specific models. Giza enables non-custodial agents to execute complex DeFi strategies based on verified generated outputs. Phala uses Intel SGX enclaves to securely store sensitive information such as private keys within AI agents.
3. Core DeCC Ecosystem Classification
On-chain privacy generally refers to Decentralized Confidential Computing Networks (DeCC). While markets often tend to classify protocols based on the underlying privacy technology, each privacy stack has its tradeoffs, and more protocols adopt hybrid approaches in their privacy solutions. Therefore, it is best to classify them into privacy blockchains, privacy middleware, and privacy applications.
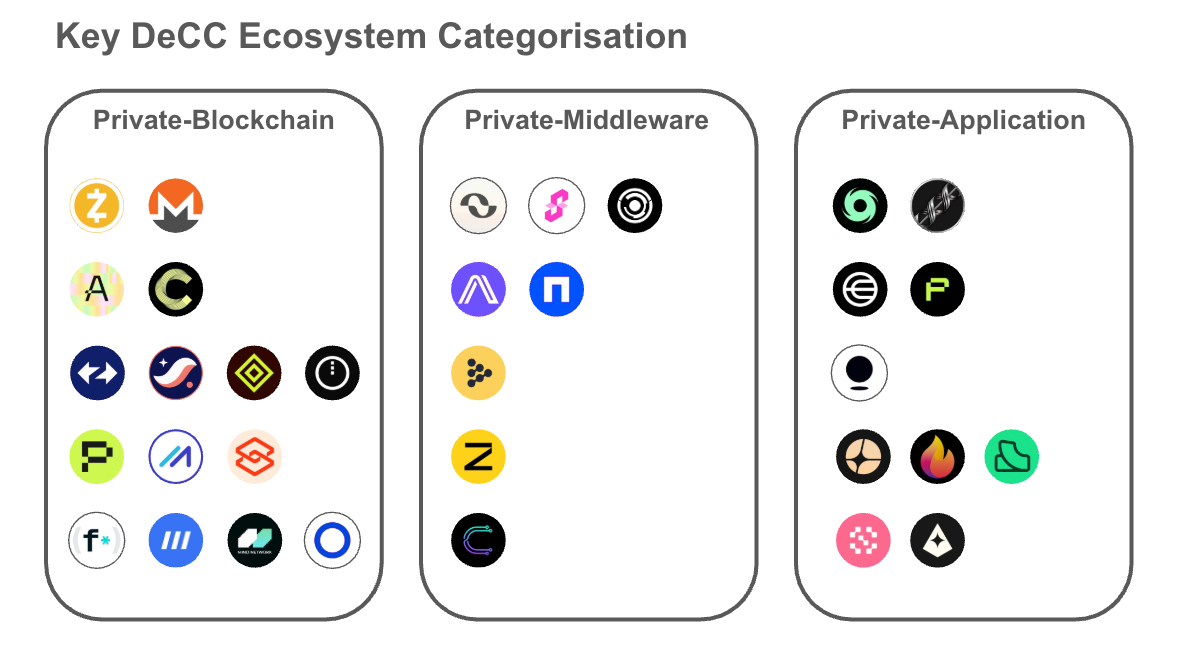
Core DeCC Ecosystem Classification
3.1. Privacy Blockchains
The "privacy blockchain" category includes layer-1 and layer-2 networks where privacy mechanisms are written into the consensus or execution environment. The core challenges for these networks are the "cross-chain barriers". Users and liquidity must be attracted to migrate from established blockchains, which is extremely difficult without killer applications making the migration economically feasible. Privacy layer network tokens are often assigned a "layer-one network premium", as they serve as collateral to secure the network and as gas tokens.
3.1.1 The Legacy and Evolution of Layer-1 Network Privacy
Zcash has historically positioned itself as Bitcoin with privacy features. The network has a dual address system that allows users to switch between public and private transactions and includes a "view key" for decrypting transaction details for compliance purposes.
The protocol is transitioning from proof-of-work (PoW) consensus to a hybrid model called Crosslink, which will integrate proof-of-stake (PoS) elements by 2026, providing faster certainty than the original probabilistic certainty of Nakamoto consensus. After the halving event in November 2024, the next halving is expected to occur in November 2028.
On the other hand, Monero maintains its default privacy mode, using ring signatures, stealth addresses, and ringCT to enforce privacy on each transaction. This design choice has led most exchanges to delist XMR tokens from their platforms in 2024. Additionally, Monero experienced several hash power attacks in 2025 resulting in reorganizations of up to 18 blocks, erasing approximately 118 confirmed transactions.
Secret Network is a TEE-based privacy layer-1 network established in 2020 on the Cosmos SDK, equipped with view keys for access control. Secret positions itself not just as a standalone chain, but also as TEE-as-a-service for EVM and IBC chains. The team also focuses on providing confidential computing in AI and is exploring the integration of threshold FHE into the network.
Canton Network is supported by Wall Street giants like Goldman Sachs, JPMorgan, Citi Ventures, Blackstone, BNY, Nasdaq, and S&P Global. It is a layer-1 network blockchain designed to introduce trillions of dollars in RWA (real-world assets) through a unique privacy feature called the Daml Ledger Model. Parties in the Daml ledger can only view subsets of the ledger connected to their subnetwork, allowing only involved parties in transactions to validate, with unrelated parties actually unaware of the existence of transactions.
Aleo is a ZK layer-one network that compiles code into ZK circuits using a proprietary Rust-based language, Leo. Users generate proofs of transaction execution off-chain (or pay miners to generate them) and only send the encrypted proof to the network.
Inco positions itself as an FHE layer-one network while also providing FHE-as-a-Service to other chains through cross-chain bridges and messaging protocols. This same functionality allows the chain to service deep liquidity without needing to build its own DeFi from scratch.
Octra is a high-performance FHE layer-one network. Octra has built its proprietary cryptography from the ground up, called Hypergraph FHE (HFHE), allowing parallel processing in the computation process, achieving peak throughput of 17,000 TPS in its testnet.
Mind Network utilizes restaking protocols like EigenLayer to protect the FHE validator network. The protocol aims to create an end-to-end encrypted internet HTTPZ and enable AI agents to manage encrypted data.
3.1.2. The ZK-layer Two Networks
ZKsync has evolved from simple scaling to implementing a range of comprehensive solutions, such as Prividium, ZKsync Interop, and Airbender. Prividium allows companies to execute transactions privately while still using Ethereum for final settlement. Airbender is a high-performance RISC-V zkVM prover that generates ZK proofs in less than a second. ZKsync Interop allows users to provide collateral on ZK chains and borrow assets on Ethereum.
Starknet leverages STARKs (Scalable Transparent Argument of Knowledge) for high-throughput scaling and features native account abstraction capabilities. Each account on Starknet is a smart contract, allowing the execution of concealed transactions using account contracts. The team has also proposed a layer-two network Ztarknet that settles on Zcash, introducing a smart contract platform benefiting from Zcash's anonymity.
Aztec operates as a native privacy layer-two network on Ethereum, processing encrypted data with a UTXO-like note system while handling public data with an account-based system. Aztec's architecture, based on Noir, relies on client-side proofs or privacy execution environments (PXE), with users generating ZK proofs locally on their devices before sending them to the network.
Midnight operates as a partner chain for Cardano, utilizing Cardano's stake pool operators (SPOs) for security while running its own execution layer. It is a ZK layer-one network based on TypeScript and selective disclosure capabilities. It uses ADA for secure staking, non-shielded NIGHT tokens for governance and staking to generate Gas (DUST), and uses shielded DUST as gas tokens.
Phala relies on TEE technologies like Intel SGX for privacy protection. The protocol has shifted to an AI coprocessor model, allowing AI agents to run within TEEs, manage private keys, and collaborate with Succinct and Conduit to migrate from Polkadot parachains to Ethereum layer-two networks using the OP Succinct stack.
Fhenix is the first fhEVM layer-two network on Ethereum, bringing encrypted computing into the Ethereum ecosystem. Transactions executed on this chain are MEV protected since transaction inputs are encrypted in the memory pool.
3.2. Privacy "Middleware"
“Privacy middleware” protocols operate on a privacy-as-a-service (PaaS) model, providing computing power for proof generation, encryption, or validation. This field is highly competitive in terms of latency, cost efficiency, and network support.
Boundless is a decentralized ZK proof market, incubated by RISC Zero as a “universal ZK computing layer”. It allows any blockchain or application to outsource heavy proof computations to Boundless.
Succinct Labs is a direct competitor to Boundless, positioning itself as a high-performance prover network. It adds dedicated circuits for common tasks like hashing and signature verification to its zkVM (SP1), making its proof generation faster and cheaper.
Brevis, acting as a ZK coprocessor, allows smart contracts to query historical data from any blockchain trustlessly. Today, Brevis is expanding to a general zkVM via Pico, which can also integrate as dedicated circuits for heavy workloads.
Arcium serves as an adjustable-performance MPC solution for applications on any chain, though it uses Solana for staking, penalties, and node coordination.
Nillion also provides high-performance MPC services for applications. Its Nil Message Compute (NMC) and Nil Confidential Compute (nilCC) allow sharded data to be processed securely within TEE during computation stages without needing to send messages to each other.
iExec RLC has been a long-standing DePIN protocol providing cloud computing resources since 2017. Now it shifts focus to TEE-based confidential computing, allowing AI models to be trained or queried without revealing data inputs and providing privacy tasks to chains, including Ethereum and Arbitrum.
Marlin has also undergone a significant transformation, shifting from a blockchain CDN to a confidential computing layer (Oyster), and building a ZKP market (Kalypso) atop its computing layer.
Zama is a leading FHE protocol constructing fhEVM, TFHE-rs, and Concrete, used by protocols like Fhenix and Inco. Zama also offers FHE-as-a-Service on existing public blockchains. With the recent acquisition of Kakarot, it plans to integrate FHE into zkVM.
Cysic builds physical hardware (ASICs) to accelerate ZKP generation, reducing proof generation time from minutes to mere milliseconds. Users can request proof generation from ZK Air (consumer-grade) or ZK Pro (industrial-grade ASIC).
3.3. Privacy Applications
This is the largest category among privacy blockchains and privacy middleware, with the list in this document showing only a small fraction of it. The protocols here leverage ZK, MPC, TEE, or MPC to improve their product's user experience. Successful applications will abstract the complexity of privacy protection and provide genuine product-market fit solutions.
Tornado Cash is the original decentralized and immutable mixer. The protocol was sanctioned by the US Treasury in 2022 but had those sanctions lifted in early 2025. Nevertheless, it remains a high-risk tool for compliant entities.
Railgun is notably recognized by Vitalik Buterin. It offers a voluntary disclosure shielded transaction solution that goes beyond Tornado Cash by integrating user’s "safes" with DeFi protocols like Uniswap or Aave. Although its shielded assets constitute only around 20% of Tornado Cash, it is still widely considered a potential competitor.
World (formerly Worldcoin) establishes "personhood proofs" via iris scanning, with biometric data encrypted, sending only ZKPs to the network. World ID has become an effective tool for distinguishing between bots and AI.
zkPass allows users to generate proofs of their personal identity and media profile data via third-party TLS handshake, enabling access to gated applications without disclosing private information.
Privy enables users to seamlessly log in to decentralized applications using their email or Web2 accounts, creating MPC wallets where keys are split between user devices and secure servers. This essentially eliminates cumbersome seed phrase backups and significantly improves user experience.
Aster partnered with Brevis to build its Aster Chain, providing privacy transaction features on top of its existing hidden orders. The protocol's roadmap indicates that Aster Chain is expected to launch in the first quarter of 2026.
Malda is a unified liquidity lending protocol that utilizes Boundless proofs to manage user lending positions across multiple blockchains.
Hibachi offers a high-frequency decentralized perpetual exchange and leverages Succinct proofs for its off-chain central limit order book (CLOB) for on-chain verification.
Giza introduces machine learning to smart contracts, permitting them to run verifiable outputs originating from expected AI models. This makes it possible for AI-driven DeFi strategies to execute on-chain without manipulation.
Sentient is a dedicated layer-one network for AI (supported by Polygon CDK) aiming to create an open AGI platform and appropriately rewards contributors. Owners of AI models upload their proprietary AI models to the network and earn rewards based on usage. Models on the platform have encrypted fingerprints ensuring that certain outputs are produced by specific models. It also builds the Sentient Enclaves Framework, leveraging AWS Nitro Enclaves to realize confidential computing in AI models, shielding user prompts and the internal states of models from node operators.
4. Current Trends and Future Outlook
4.1.1. The Rise of Privacy Middleware
We are witnessing a shift from monolithic privacy chains to modular privacy layers. Protocols can deploy on any established blockchain (like Ethereum and Solana) while accessing privacy services through smart contracts, thus minimizing the barrier to accessing protocols. Additionally, with the growing demand for privacy features and the increasing privacy awareness in the industry, privacy middleware is the ultimate beneficiary, as running one's computationally intensive confidentiality framework is economically unreasonable for many startup protocols.
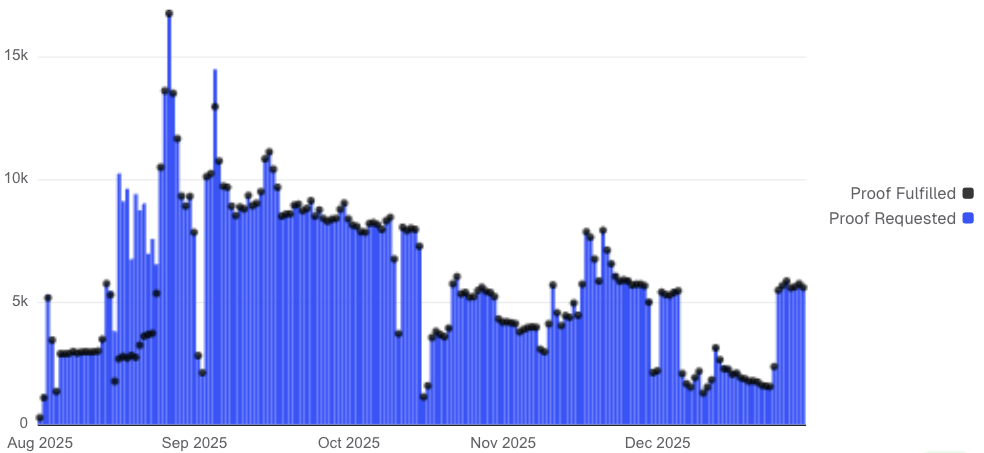
Number of proof requests and completions on Succinct, Source: Dune
4.1.2. Hybrid Solutions
Current privacy-enhancing technologies come with their own limitations. For instance, ZKP cannot perform computations on encrypted data, MPC may face latency restrictions when the number of participants is high, TEE could be compromised through fault injection and side-channel attacks (attacker gains physical access to hardware), while in FHE computation, complex calculations may take longer and carry a higher risk of data corruption due to accumulated noise. Therefore, more protocols tend to mix their privacy tools or design dedicated hardware for optimizing computations.
4.1.3. Confidential and Verifiable AI
According to Morgan Stanley, global capital expenditure related to AI is expected to reach $3 trillion. As demand for AI is anticipated to expand in 2026, confidential and verifiable AI has emerged as a major trend for 2025 and is expected to scale up in 2026. Conducting confidential model training on sensitive data such as medical and financial records may mark another key milestone in decentralized AI.
5. Conclusion
The era of privacy tokens lacking a “view key” may soon come to an end. The industry bets that this "selective disclosure" approach will be accepted as a sufficient compromise. Should regulators later reject this approach, it may force networks to opt for "regulated permissioned chains" for anonymity.
The maturation of privacy-enhancing technologies is key to unlocking "trillions of dollars" in traditional finance. Bonds, securities, and corporate payrolls cannot exist on transparent chains. As these protocols demonstrate their robustness in 2025, we expect the first major pilots of "privacy RWA" to launch on one of the aforementioned networks in 2026.
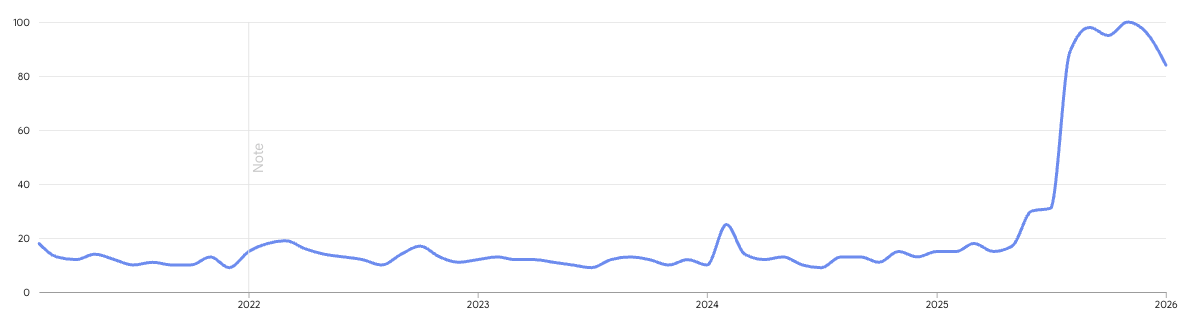
Google trends for "blockchain privacy" over the past 5 years, Source: Google
The heat of blockchain privacy may temporarily cool, but demand for privacy features at the application layer is expected to grow steadily, significantly improving user experience to attract a large audience not native to crypto. This marks the moment when on-chain privacy transitions from "optional" to "essential".
免责声明:本文章仅代表作者个人观点,不代表本平台的立场和观点。本文章仅供信息分享,不构成对任何人的任何投资建议。用户与作者之间的任何争议,与本平台无关。如网页中刊载的文章或图片涉及侵权,请提供相关的权利证明和身份证明发送邮件到support@aicoin.com,本平台相关工作人员将会进行核查。




